If you are looking for the full AZ-104 study guide: https://www.cloud13.ch/2023/10/31/az-104-study-guide-microsoft-azure-administrator/
Learn about the various Azure networking services available that provide connectivity to your resources in Azure, deliver and protect applications, and help secure your network.
Virtual Networks
A virtual network cannot span regions or subscriptions, it has its boundaries, but can span (subnets) across availability zones in a region. Virtual networks are always IPv4 ranges, IPv6 ranges are optional.
Azure Virtual Network is a service that provides the fundamental building block for your private network in Azure. An instance of the service (a virtual network) enables many types of Azure resources to securely communicate with each other, the internet, and on-premises networks. These Azure resources include virtual machines (VMs).
A virtual network is similar to a traditional network that you’d operate in your own datacenter. But it brings extra benefits of the Azure infrastructure, such as scale, availability, and isolation.
A training module on designing and implementing core Azure networking infrastructure, including virtual networks can be found here: https://learn.microsoft.com/en-us/training/modules/introduction-to-azure-virtual-networks/
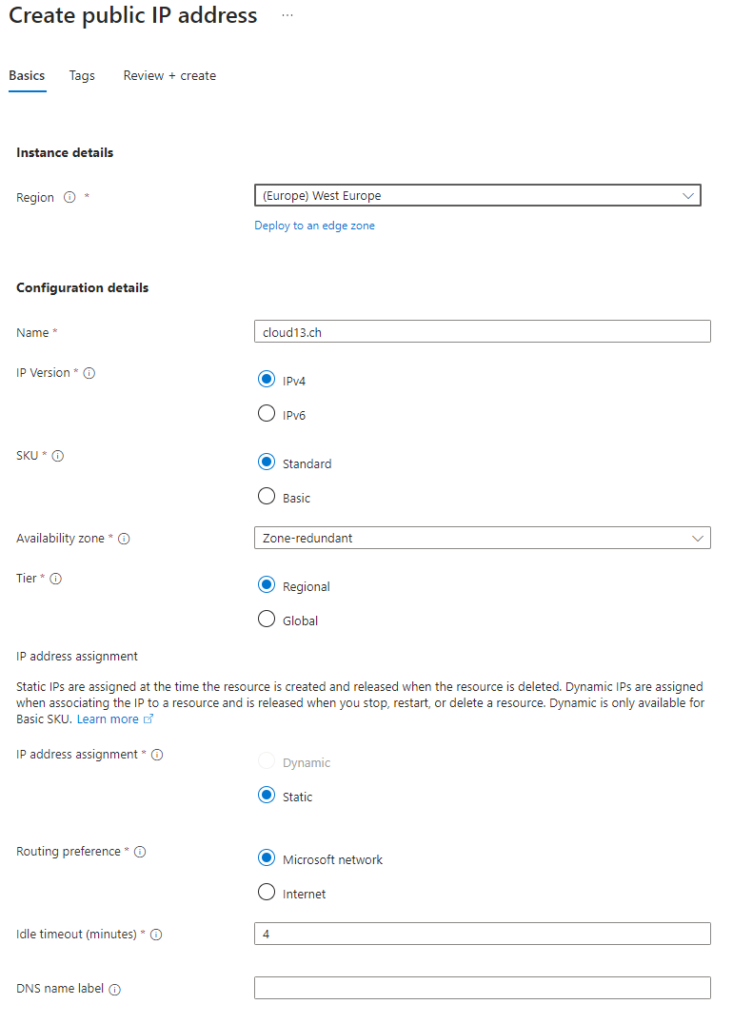
Public IPs
Public IP addresses enable Internet resources to communicate with Azure resources and enable Azure resources to communicate outbound with Internet and public-facing Azure services. A public IP address in Azure is dedicated to a specific resource, until it’s unassigned by a network engineer. A resource without a public IP assigned can communicate outbound through network address translation services, where Azure dynamically assigns an available IP address that isn’t dedicated to the resource.
In Azure Resource Manager, a public IP (this is also bound to a region) address is a resource that has its own properties. Some of the resources you can associate a public IP address resource with:
- Virtual machine network interfaces
- Virtual machine scale sets
- Public Load Balancers
- Virtual Network Gateways (VPN/ER)
- NAT gateways
- Application Gateways
- Azure Firewall
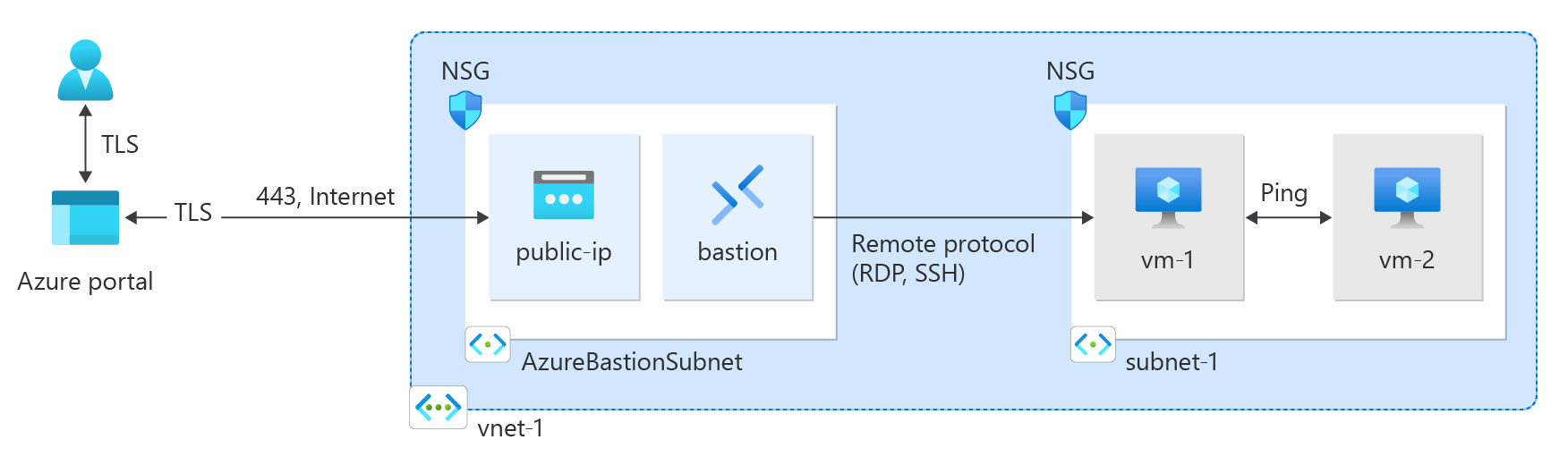
- Bastion Host
- Route Server
Public IP addresses are created with one of the following SKUs:
| Public IP address | Standard | Basic |
|---|---|---|
| Allocation method | Static | For IPv4: Dynamic or Static; For IPv6: Dynamic. |
| Idle Timeout | Have an adjustable inbound originated flow idle timeout of 4-30 minutes, with a default of 4 minutes, and fixed outbound originated flow idle timeout of 4 minutes. | Have an adjustable inbound originated flow idle timeout of 4-30 minutes, with a default of 4 minutes, and fixed outbound originated flow idle timeout of 4 minutes. |
| Security | Secure by default model and be closed to inbound traffic when used as a frontend. Allow traffic with network security group (NSG) is required (for example, on the NIC of a virtual machine with a Standard SKU Public IP attached). | Open by default. Network security groups are recommended but optional for restricting inbound or outbound traffic. |
| Availability zones | Supported. Standard IPs can be nonzonal, zonal, or zone-redundant. Zone redundant IPs can only be created in regions where 3 availability zones are live. IPs created before availability zones aren’t zone redundant. | Not supported. |
| Routing preference | Supported to enable more granular control of how traffic is routed between Azure and the Internet. | Not supported. |
| Global tier | Supported via cross-region load balancers. | Not supported. |
vNet Peering
What if I have more than one network or vNets that should communicate with each other? Azure has the idea of peering that can happen in the same region or globally.
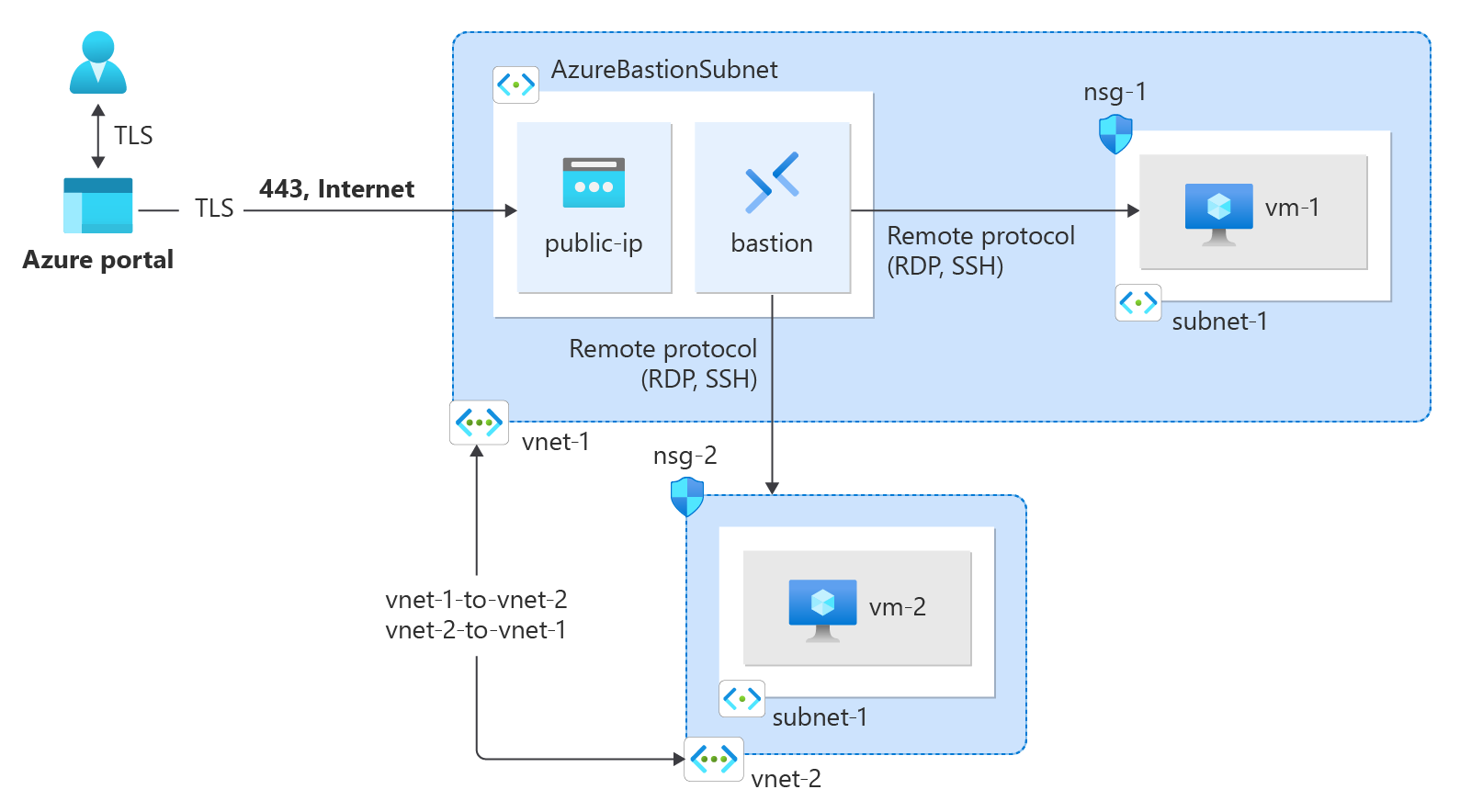
Virtual network peering enables you to seamlessly connect two or more Virtual Networks in Azure. The virtual networks appear as one for connectivity purposes. The traffic between virtual machines in peered virtual networks uses the Microsoft backbone infrastructure. Like traffic between virtual machines in the same network, traffic is routed through Microsoft’s private network only.
Azure supports the following types of peering:
-
Virtual network peering: Connecting virtual networks within the same Azure region.
-
Global virtual network peering: Connecting virtual networks across Azure regions.
Note: Network traffic between peered virtual networks is private. Traffic between the virtual networks is kept on the Microsoft backbone network. No public Internet, gateways, or encryption is required in the communication between the virtual networks.
Important: Peering connections are non-transitive! From the FAQ:
If I peer VNetA to VNetB and I peer VNetB to VNetC, does that mean VNetA and VNetC are peered?
No. Transitive peering is not supported. You must manually peer VNetA to VNetC.
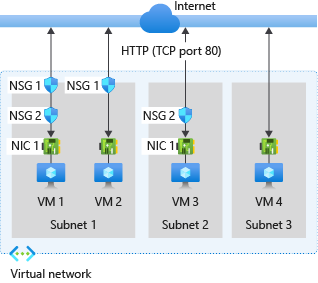
Network Security Groups
You can use an Azure network security group (NSG) to filter network traffic between Azure resources in an Azure virtual network. A network security group contains security rules that allow or deny inbound network traffic to, or outbound network traffic from, several types of Azure resources. For each rule, you can specify source and destination, port, and protocol.
A network security group contains as many rules as desired, within Azure subscription limits. Each rule specifies the following properties:
| Property | Explanation |
|---|---|
| Name | A unique name within the network security group. The name can be up to 80 characters long. It must begin with a word character, and it must end with a word character or with ‘_’. The name may contain word characters or ‘.’, ‘-‘, ‘_’. |
| Priority | A number between 100 and 4096. Rules are processed in priority order, with lower numbers processed before higher numbers, because lower numbers have higher priority. Once traffic matches a rule, processing stops. As a result, any rules that exist with lower priorities (higher numbers) that have the same attributes as rules with higher priorities aren’t processed. Azure default security rules are given the highest number with the lowest priority to ensure that custom rules are always processed first. |
| Source or destination | Any, or an individual IP address, classless inter-domain routing (CIDR) block (10.0.0.0/24, for example), service tag, or application security group. If you specify an address for an Azure resource, specify the private IP address assigned to the resource. Network security groups are processed after Azure translates a public IP address to a private IP address for inbound traffic, and before Azure translates a private IP address to a public IP address for outbound traffic. Fewer security rules are needed when you specify a range, a service tag, or application security group. The ability to specify multiple individual IP addresses and ranges (you can’t specify multiple service tags or application groups) in a rule is referred to as augmented security rules. Augmented security rules can only be created in network security groups created through the Resource Manager deployment model. You can’t specify multiple IP addresses and IP address ranges in network security groups created through the classic deployment model. |
| Protocol | TCP, UDP, ICMP, ESP, AH, or Any. The ESP and AH protocols aren’t currently available via the Azure portal but can be used via ARM templates. |
| Direction | Whether the rule applies to inbound, or outbound traffic. |
| Port range | You can specify an individual or range of ports. For example, you could specify 80 or 10000-10005. Specifying ranges enables you to create fewer security rules. Augmented security rules can only be created in network security groups created through the Resource Manager deployment model. You can’t specify multiple ports or port ranges in the same security rule in network security groups created through the classic deployment model. |
| Action | Allow or deny |
Azure Firewall and Routing
Azure Firewall is a cloud-native and intelligent network firewall security service that provides the best of breed threat protection for your cloud workloads running in Azure. It’s a fully stateful firewall as a service with built-in high availability and unrestricted cloud scalability. It provides both east-west and north-south traffic inspection. To learn what’s east-west and north-south traffic, see East-west and north-south traffic.
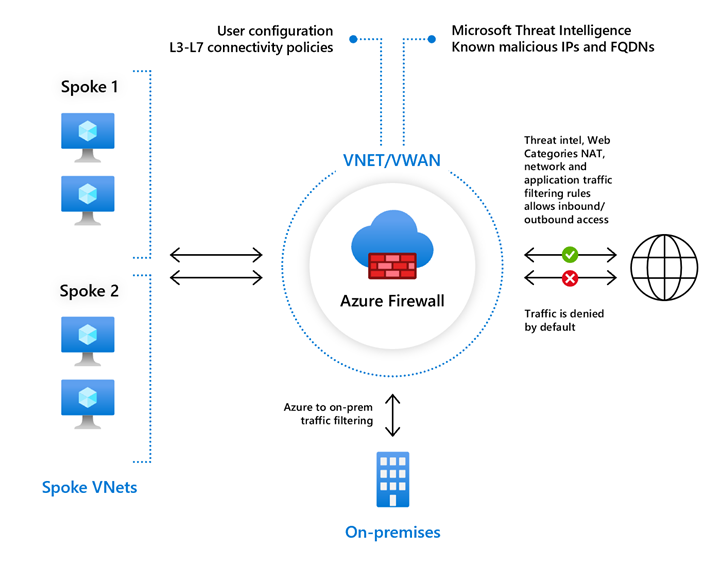
Azure Firewall includes the following features:
- Built-in high availability
- Availability Zones
- Unrestricted cloud scalability
- Application FQDN filtering rules
- Network traffic filtering rules
- FQDN tags
- Service tags
- Threat intelligence
- DNS proxy
- Custom DNS
- FQDN in network rules
- Deployment without public IP address in Forced Tunnel Mode
- Outbound SNAT support
- Inbound DNAT support
- Multiple public IP addresses
- Azure Monitor logging
- Forced tunneling
- Web categories
- Certifications
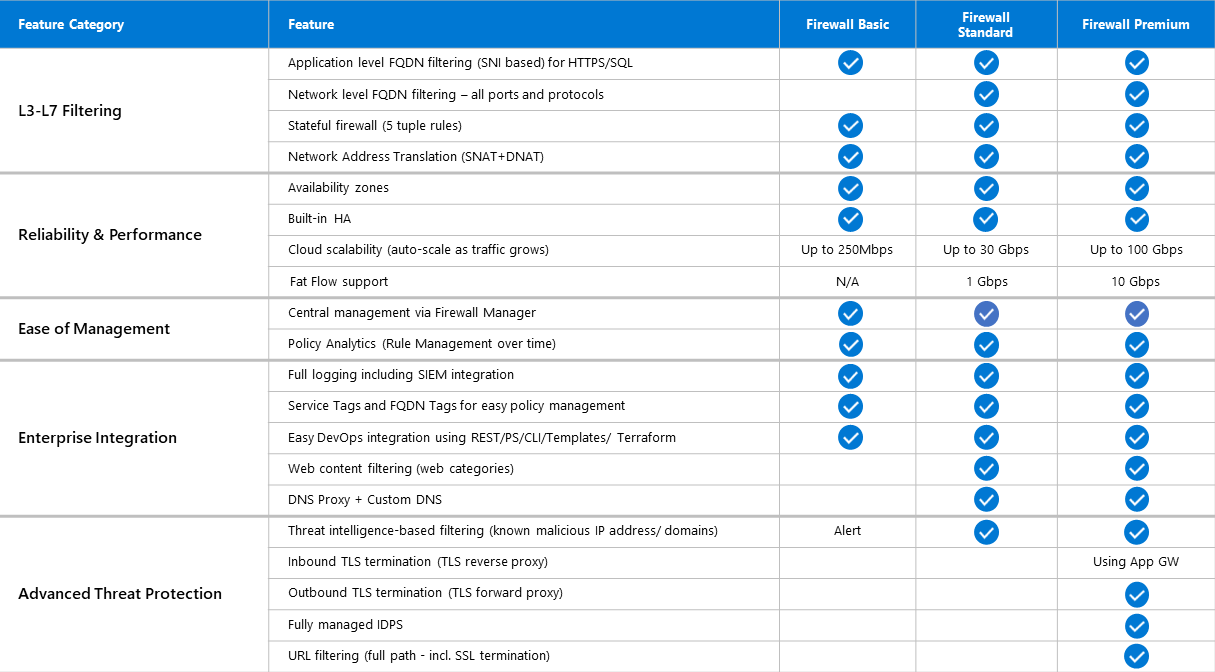
Azure Firewall now supports three different SKUs to cater to a wide range of customer use cases and preferences.
- Azure Firewall Premium is recommended to secure highly sensitive applications (such as payment processing). It supports advanced threat protection capabilities like malware and TLS inspection.
- Azure Firewall Standard is recommended for customers looking for Layer 3–Layer 7 firewall and needs autoscaling to handle peak traffic periods of up to 30 Gbps. It supports enterprise features like threat intelligence, DNS proxy, custom DNS, and web categories.
- Azure Firewall Basic is recommended for SMB customers with throughput needs of 250 Mbps.
A training module for Azure Firewalls can be found here: https://learn.microsoft.com/en-us/training/modules/introduction-azure-firewall/
User-Defined Route
To send traffic through this Azure Firewall, you can create a user-defined route (UDR).
Click here for part 2.