VMware Explore 2023 US – Day 1 Announcements
VMware Explore 2023 US is currently happening in Las Vegas and I am onsite! Below you will find an overview of the information that was shared with us during the general session and solution keynotes.
Please be aware that this list is not complete but it should include all the major announcements including references and sources.
VMware Aria and VMware Tanzu
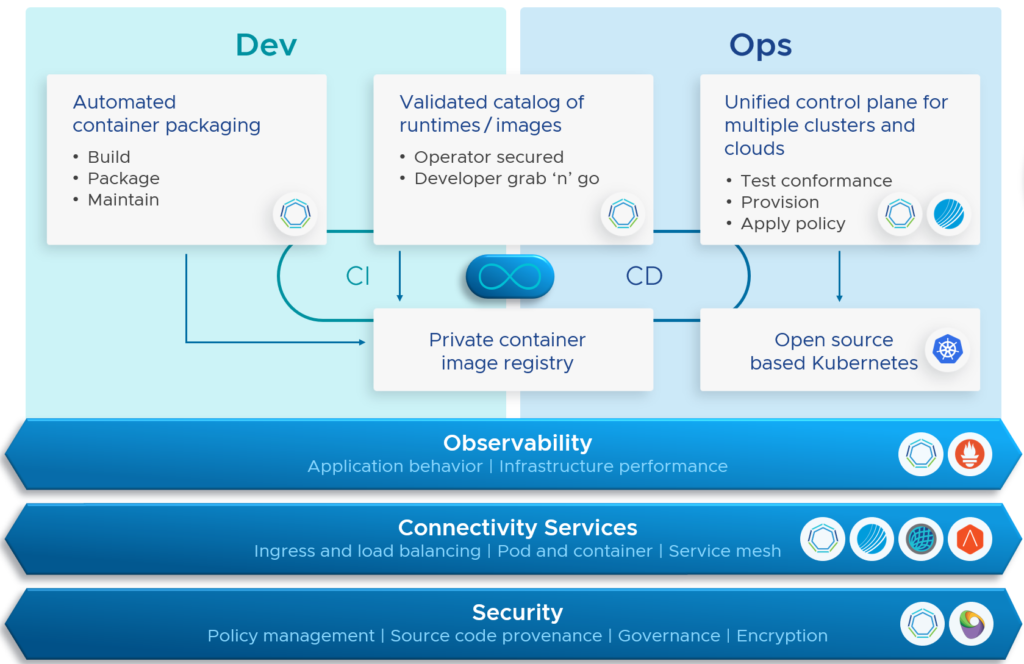
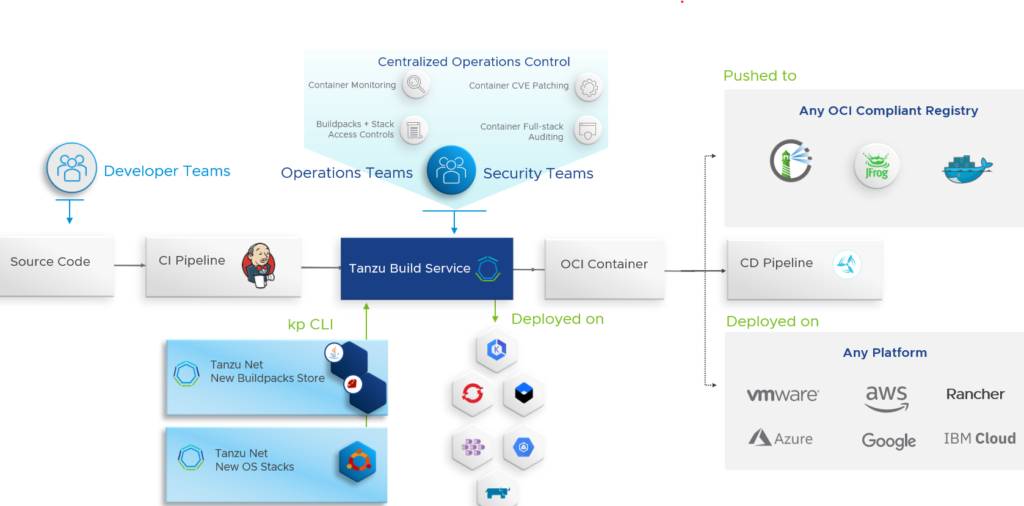
Starting this year, VMware Aria and VMware Tanzu form a single track at VMware Explore and VMware introduced the develop, operate, and optimize pillars (DOO) for Aria and Tanzu around April 2023.

The following name changes and adjustments have been announced at VMware Explore US 2023:
- The VMware Tanzu portfolio includes two new product categories (product family) called “Tanzu Application Platform” and “Tanzu Intelligence Services”.
- Tanzu Application Platform includes the products Tanzu Application Platform (TAP) and Tanzu for Kubernetes Operations (TKO), and the new Tanzu Application Engine module.
- Tanzu Intelligence Services – Aria Cost powered by CloudHealth, Aria Guardrails, Aria Insights, and Aria Migration will be rebranded as “Tanzu” and become part of this new Tanzu Intelligence Services category.
- Tanzu Hub & Tanzu Graph
- Tanzu CloudHealth
- Tanzu Guardrails
- Tanzu Insights (currently known as Aria Insights)
- Tanzu Transformer (currently known as Aria Migration)
- Aria Hub and Aria Graph are now called Tanzu Hub
- VMware Cloud Packs are now called the VMware Cloud Editions (more information below)
Note: VMware expects to implement these changes latest by Q1 2024
The VMware Aria and Tanzu announcement and rebranding information can be found here.
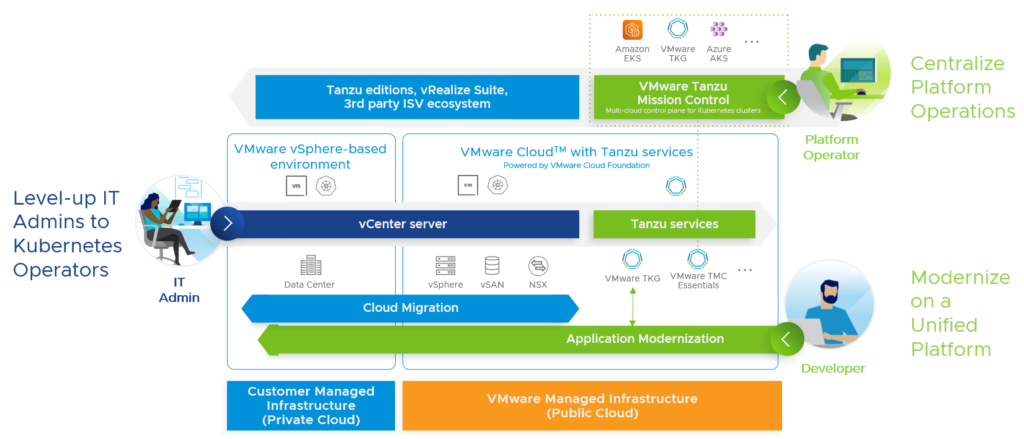
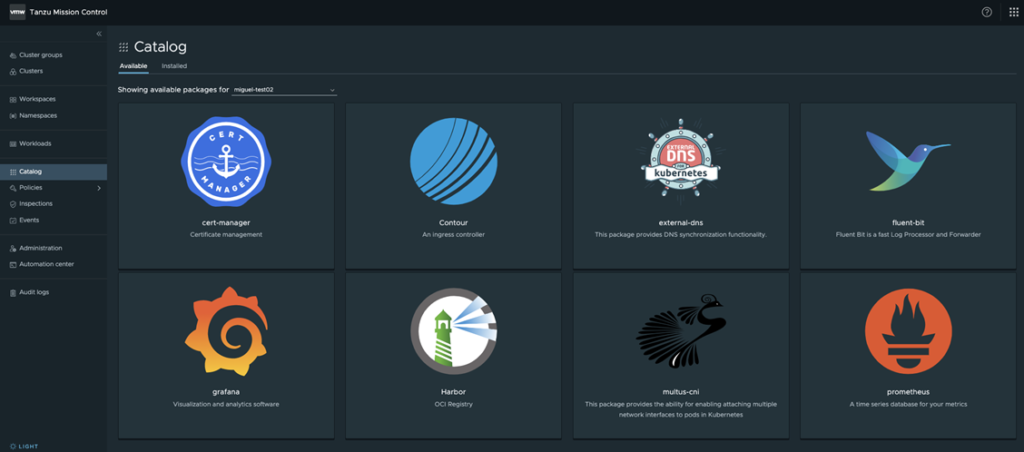
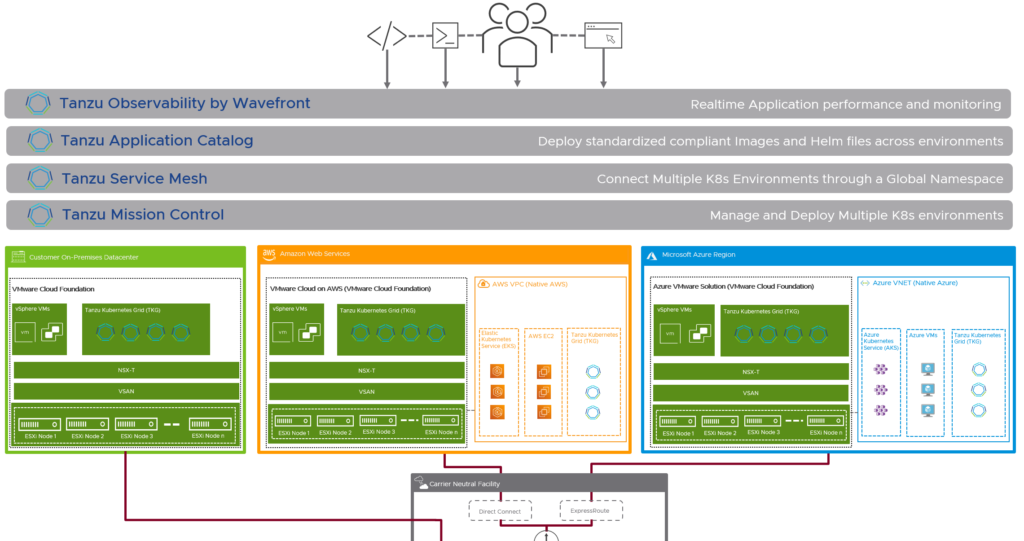
Tanzu Mission Control
After the announcement that Tanzu Mission Control supports the lifecycle management of Amazon EKS clusters, VMware announced the expansion to provide lifecycle management capabilities of Microsoft AKS clusters now as well.
Tanzu Application Engine (Private Beta)
VMware announced a new solution for the Tanzu Application Platform category.
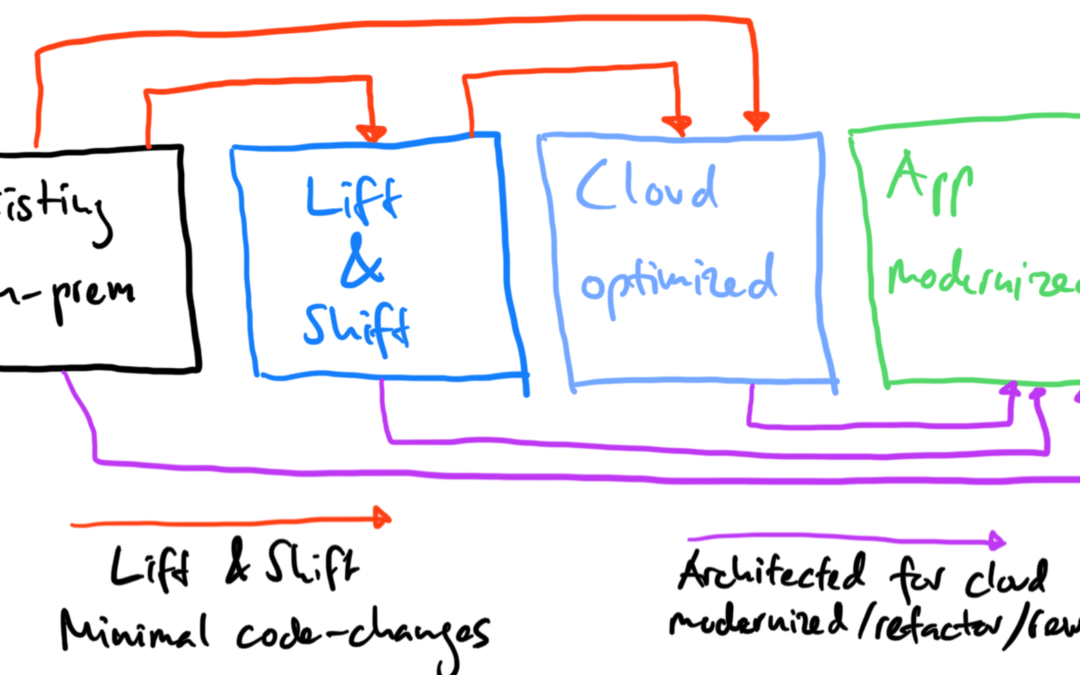
VMware Tanzu for Kubernetes Operations is introducing Tanzu Application Engine, enhancing multi-cloud support with lifecycle management of Azure AKS clusters, and offering new Kubernetes FinOps (cluster cost) visibility. A new abstraction that includes workload placement, K8s runtime, data services, libraries, infra resources, with a set of policies and guardrails.
The Tanzu Application Engine announcement can be found here.
VMware RabbitMQ Managed Control Plane
I know a lot of customers who built an in-house RabbitMQ cloud service.
VMware just announced a beta program for a new VMware RabbitMQ Managed Control Plane which allows enterprises to seamlessly integrate RabbitMQ within their existing cloud environment, offering flexibility and control over data streaming processes.
What’s New with VMware Aria?
Other Aria announcements can be found here.
What’s New with VMware Aria Operations at VMware Explore
Next-Gen Public Cloud Management with VMware Aria Automation
VMware Cloud Editions
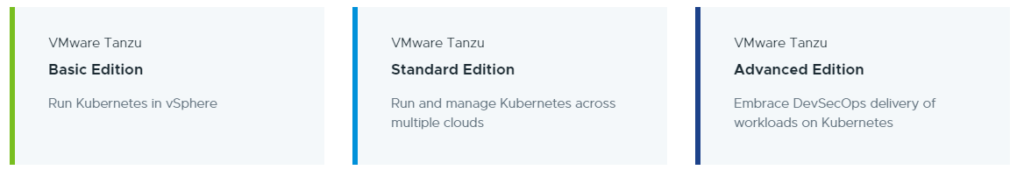
What has started with four different VMware Cloud Packs, is now known as “VMware Cloud Editions” with five different options:

Here’s an overview of the different solutions/subscriptions included in each edition:

More VMware Cloud related announcements can be found here.
What’s New in vSphere 8 Update 2
As always, VMware is working on enhancing operational efficiency to make the life of an IT admin easier. And this gets better with the vSphere 8 U2 release.
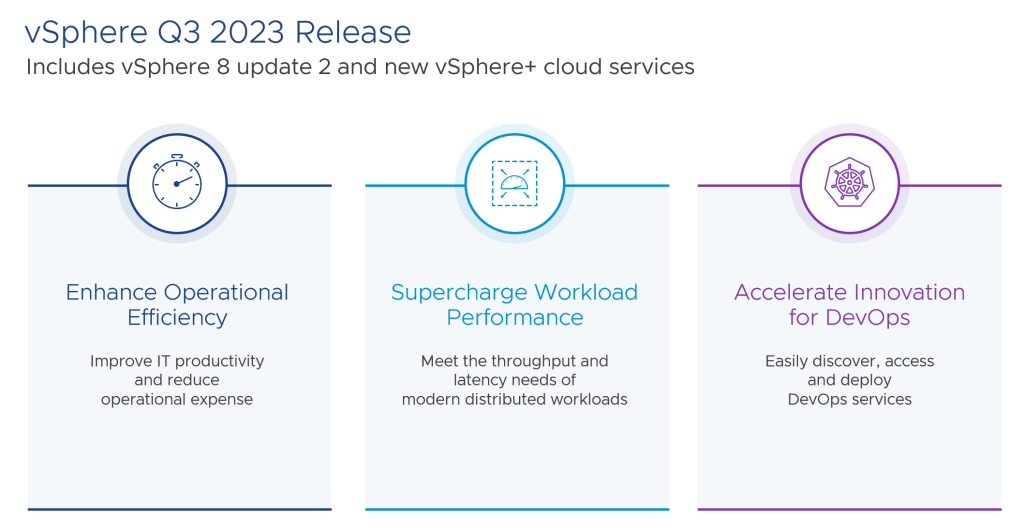
In vSphere 8 Update 2, we are making significant improvements to several areas of maintenance to reduce and in some cases eliminate this need for downtime so vSphere administrators can make those important maintenance changes without having a large impact on the wider vSphere infrastructure consumers.
These enhancements include, reduced downtime upgrades for vCenter, automatic vCenter LVM snapshots before patching and updating, non-disruptive certificate management, and reliable network configuration recovery after a vCenter is restored from backup.
More information about the vSphere 8 Update 2 release can be found here.
What’s New in vSAN 8 Update 2
At VMware Explore 2022, VMware announced the new vSAN 8.0 release which included the new Express Storage Architecture (ESA), which even got better with the recent vSAN 8.0 Update 1 release.
VMware vSAN Max – Petabyte-Scale Disaggregated Storage
VMware vSAN Max, powered by vSAN Express Storage Architecture, is a new vSAN offering in the vSAN family delivering
petabyte-scale disaggregated storage for vSphere. With its new disaggregated storage deployment model, vSAN customers can scale storage elastically and independently from compute and deploy unified block, file, and partner-based object storage to maximize utilization and achieve lower TCO.

vSAN Max expands the use cases in which HCI can provide exceptional value. Disaggregation through vSAN Max provides flexibility to build infrastructure with the scale and efficiency required for non-linear scaling applications, such as storage-intensive databases, modern elastic applications with large datasets and more. Customers have a choice of deploying vSAN in a traditional model or a disaggregated model with vSAN Max, while still using a single control plane to manage both deployment options.
The vSAN Max announcement can be found here.
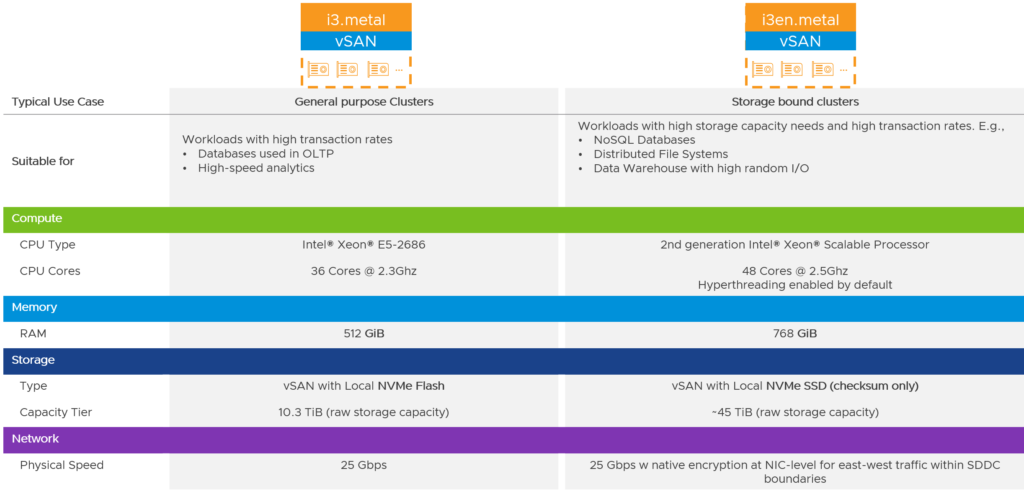
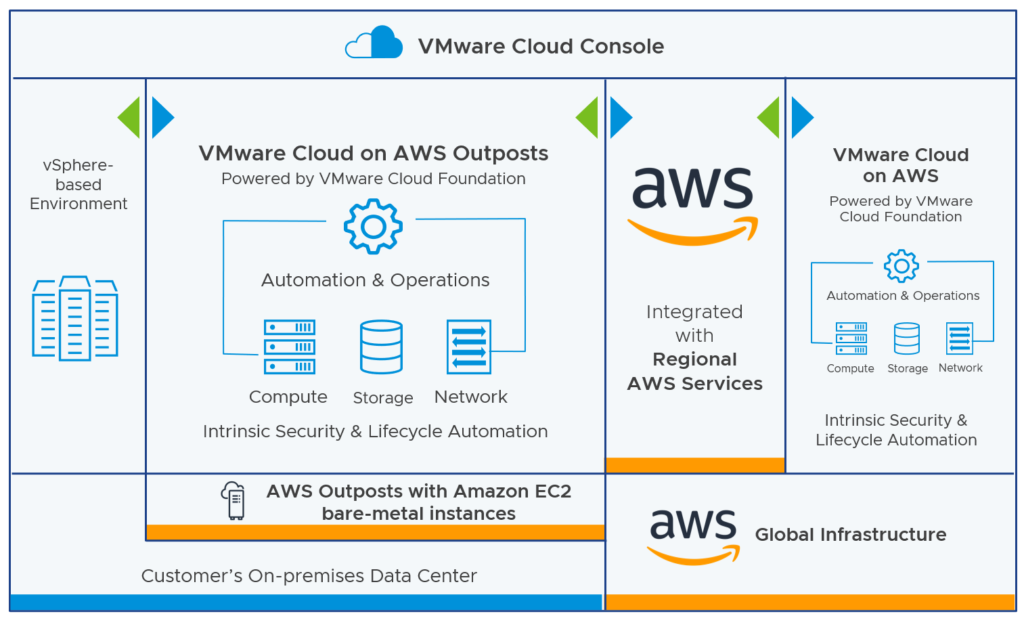
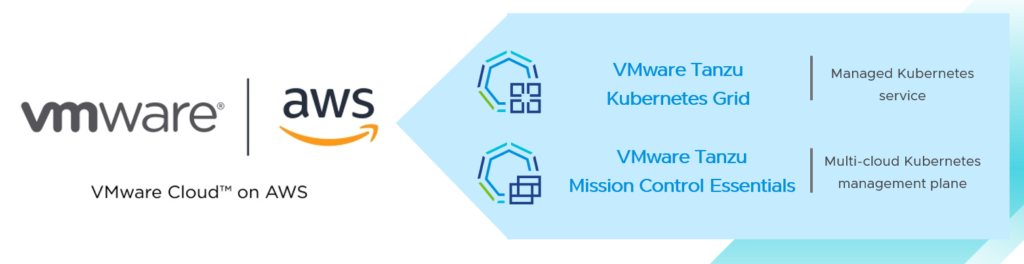
VMware Cloud on AWS
VMware announced a VMware Cloud on AWS Advanced subscription tier that will be available on i3en.metal and i4i.metal instance types only. This subscription will include advanced cloud management, networking and security features:
- VMware NSX+ Services (NSX+ Intelligence, NDR capabilities, NSX Advanced Load Balancer)
- vSAN Express Storage Architecture Support
- VMware Aria Automation
- VMware Aria Operations
- VMware Aria Operations for Logs
Note: Existing deployments (existing SDDCs) will be entitled to these advanced cloud management, networking and security features over time
The VMware Cloud on AWS Advanced Subscription Tier FAQ can be found here.
Introduction of VMware NSX+
Last year, VMware introduced Project Northstar as technology preview:
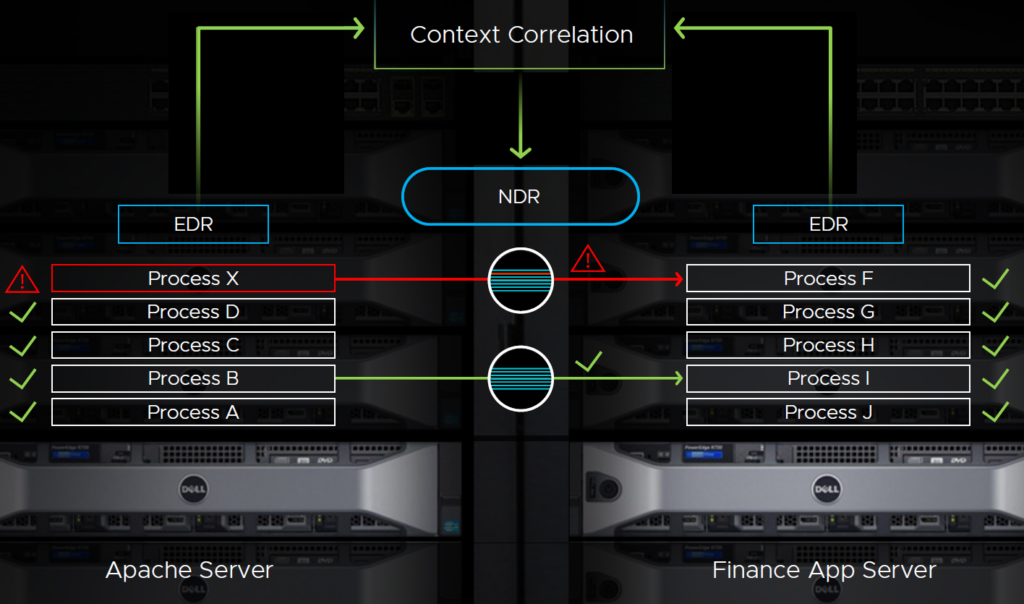
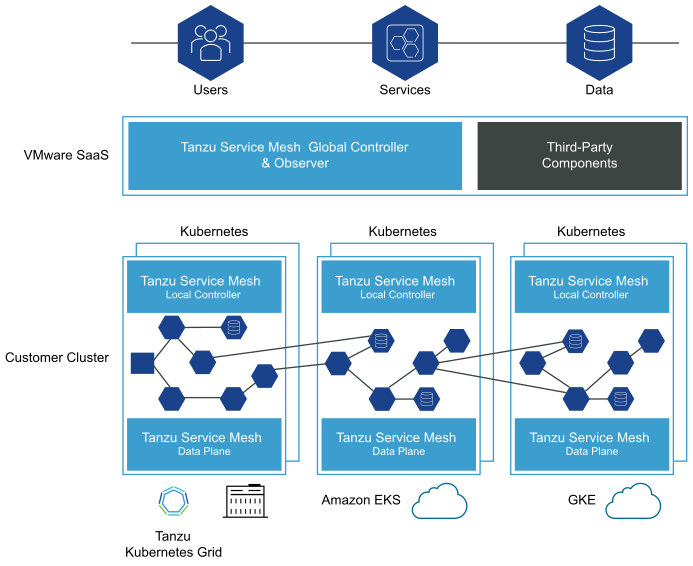
Project Northstar is a SaaS-based networking and security offering that will empower NSX customers with a set of on-demand multi-cloud networking and security services, end-to-end visibility, and controls. Customers will be able to use a centralized cloud console to gain instant access to networking and security services, such as network and security policy controls, Network Detection and Response (NDR), NSX Intelligence, Advanced Load Balancing (ALB), Web Application Firewall (WAF), and HCX. It will support both private cloud and VMware Cloud deployments running on public clouds and enable enterprises to build flexible network infrastructure that they can spin up and down in minutes.
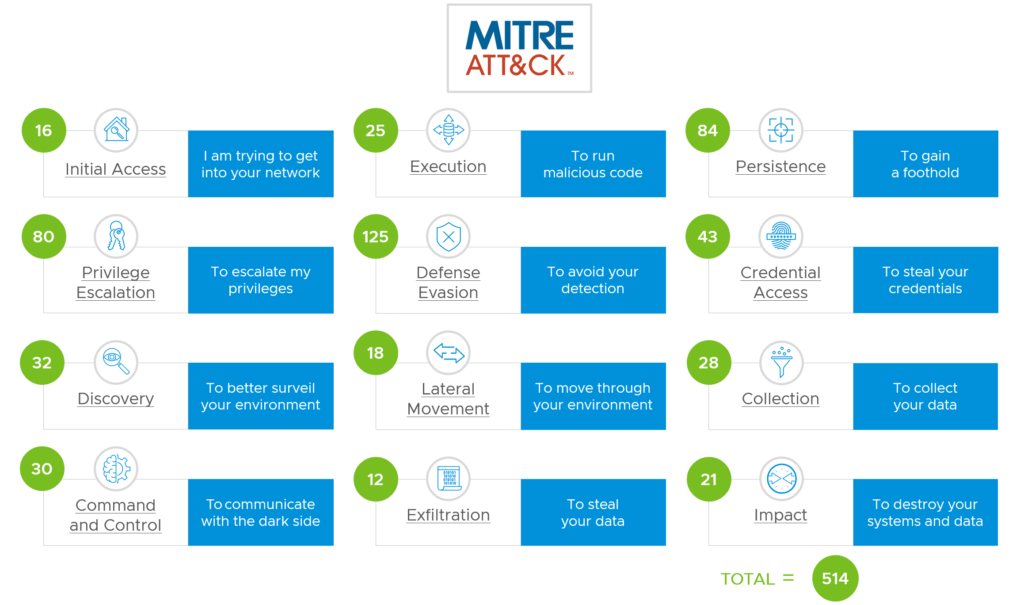
This year, VMware announced the initial availability of the NSX+ service. VMware NSX+ is a fully managed cloud-based service offering that allows networking, security, and operations teams to consume and operate VMware NSX services from a single cloud console across private and public clouds.

The following services are available:
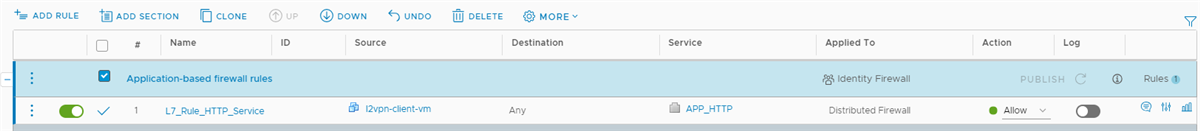
- NSX+ Policy Management: Provides unified networking and security policy management across multiple clouds and on-premises data centers.
- NSX+ Intelligence (Tech Preview only): Provides a big data reservoir and a system for network and security analytics for real-time traffic visibility into applications traffic all the way from basic traffic metrics to deep inspection of packets.
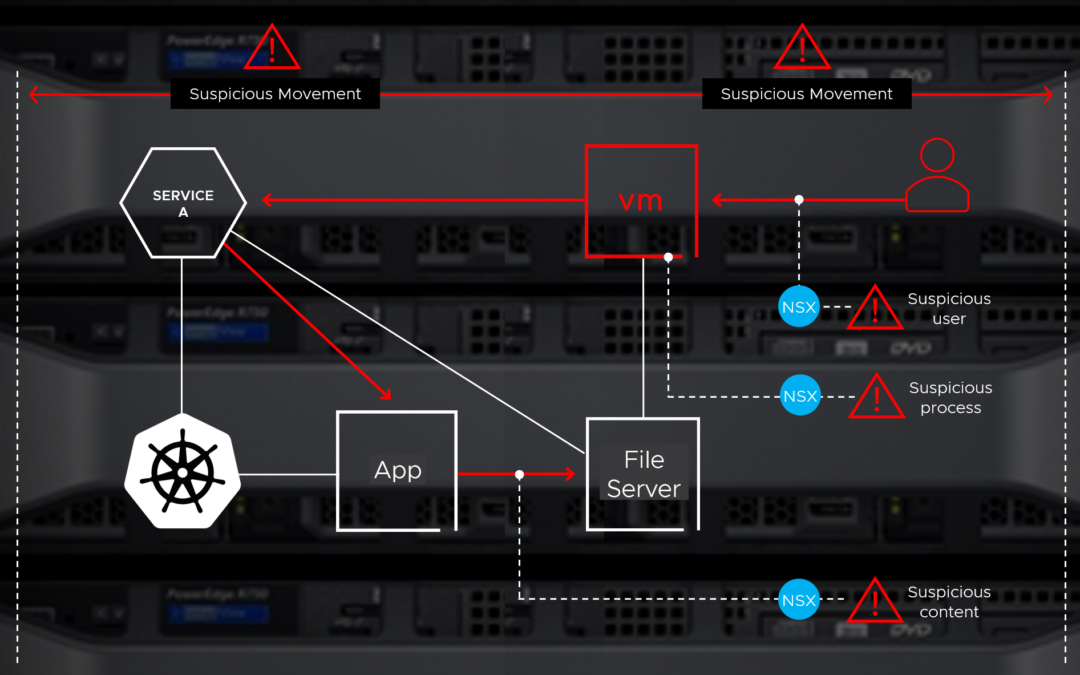
- NSX+ NDR (Tech Preview only): Provides a scalable threat detection and response service offering for Security Operations Center (SoC) teams to triage real time security threats to their data center and cloud.
There are three different NSX+ and two NSX+ distributed firewall editions available:
- NSX+ Standard. For organizations needing a basic set of NSX connectivity and security features for single location software-defined data center deployments.
- NSX+ Advanced. For organizations needing advanced networking and security features that are applied to multiple sites. This edition also entitles customers to VMware NSX+ Advanced Load Balancer Cloud Services.
- NSX+ Enterprise. For organizations needing all of the capability NSX has to offer. This edition also entitles customers to VMware NSX+ Advanced Load Balancer Cloud Services.
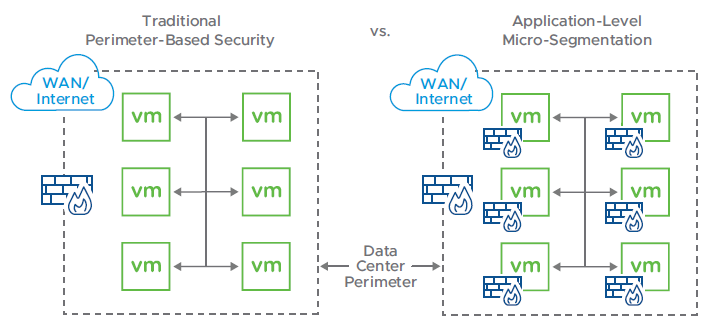
- NSX+ Distributed Firewall. For organizations needing implement access controls for east-west traffic within the network (micro-segmentation) but not focused on Threat detection and prevention services.
- NSX+ Distributed Firewall with Threat Prevention. For organizations needing access control and select Threat prevention features for east-west traffic within the network.
An NSX+ feature overview can be found here.
Note: Currently, NSX+ only supports NSX on-premises deployments (NSX 4.1.1 or later) and VMware Cloud on AWS
VMware Cloud Foundation
VMware announced a few innovations for H2 2023, which includes the support for Distributed Service Engine (DSE aka Project Monterey), vSAN ESA support, and NSX+.

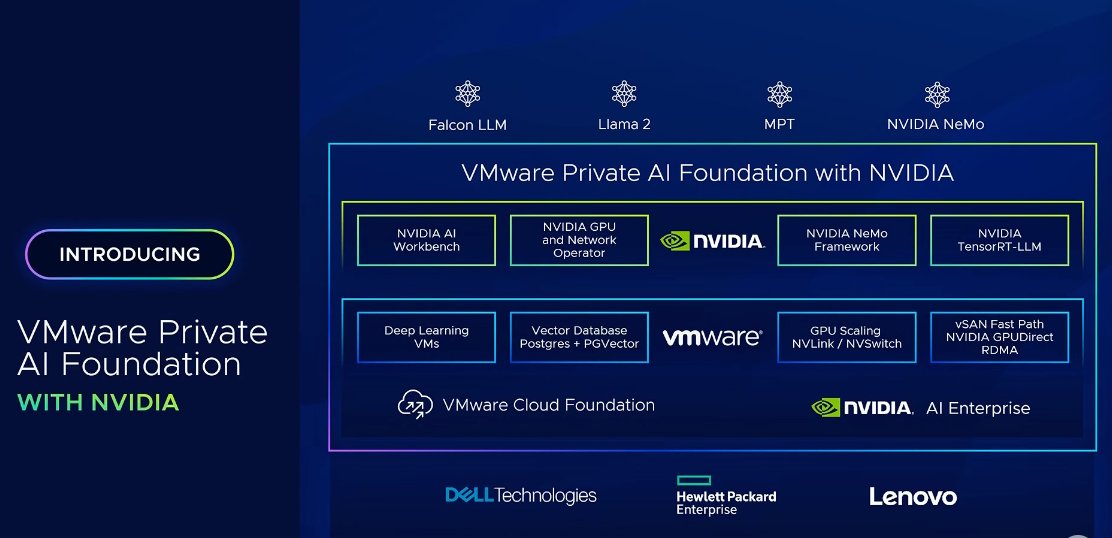
Generative AI – VMware Private AI Foundation with Nvidia
VMware and Nvidia’s CEOs announced VMware Private AI Foundation as the result of their longstanding partnership.
Built on VMware Cloud Foundation, this integrated solution with Nvidia will enable enterprises to customize models and run generative AI applications, including intelligent chatbots, assistants, search, and summarization.
Anywhere Workspace Announcements
At VMware Explore 2022, VMware shared its vision for autonomous workspaces.
Autonomous workspace is a concept (not an individual product) that is our north star for the future of end-user computing. It means going beyond creating a unified workspace with basic automations, to analyzing huge amounts of data with AI and machine learning, to drive more advanced, context aware automations. This leads to a workspace that can be considered self-configuring, self-healing, and self-securing.
VMware continued working on the realization of this vision and came up with a lot of announcements, which can be found here.
Other Announcements
Please find below some announcements that VMware shared with us during the SpringOne event or before and after the general session on August 22nd, 2023:
- Announcing Streamlined and Enhanced Cloud Migrations with Azure Spring Apps Enterprise Tier
- How Spring Solutions Can Help Improve Your Development
- Announcing Streamlined and Enhanced Cloud Migrations with Azure Spring Apps Enterprise Tier
- Introducing VMware Tanzu Developer Portal: Empowering Developers with Enterprise-Grade Backstage
- Announcing VMware Greenplum 7: The Next Big Leap in Data Warehousing, Big Data Analytics, and AI/ML
- Announcing: VMware Cloud Foundation and Lenovo ThinkAgile VX joint solution for modernizing your IT infrastructure
- What’s New in VMware Cloud Flex Storage? Major Updates Coming!
- Manage the Software-Defined Edge with VMware Edge Cloud Orchestrator
- Oracle Cloud Infrastructure Joins VMware Cloud Universal Program
- VMware Explore 2023: Innovations in Ransomware and Disaster Recovery
- VMware Ransomware Recovery Now Protects Google Cloud VMware Engine Workloads
- Edge Management at Scale: Announcing free availability of VMware Project Keswick