No, this is not an article about Citrix vs. Horizon and which product is better. And I think that you should not compare Citrix and VMware anymore. If you are still reading and haven’t closed the tab in your browser yet, you made the right decision. The intent of this article is to help you better understand when the usage of Citrix Virtual Apps and Desktops (CVAD) makes sense, which VMware products could complement a CVAD infrastructure and the different options you have with VMware Horizon.
I think it is a very big plus that I worked for Citrix before and still have some technical knowledge. This gives me more credibility in front of the customer and I am not just someone from a vendor, who tries to blame or downplay the other competitor to sell his on stuff. In fact, I always tell my customers how good Citrix is – there is no doubt about that.
But people are still stuck in the past and have the knowledge from four or six years ago. VMware Horizon has evolved into a very mature virtual apps and desktops solution and at the same time VMware’s products evolved as well and the story and product portfolio are better than ever.
Would have asked me a few years ago, no matter if I would be still with Citrix or already with VMware, VMware Horizon had some serious (feature) gaps and differences (e.g. display protocol) compared to Citrix. But Horizon has transformed into a equal player in the market and can do almost the same as CVAD (formerly XenDesktop and XenApp).
Note: I’m not saying that VMware Horizon has reached feature parity compared to Citrix
Let’s see which enhancements or new features have been released in the last 18 months for Horizon:
- A lot of enhancements and closed feature gaps for the Horizon HTML5 console (now default)
- RDS Drain Mode and RDSH Load Balancing configurable from UI
- Improved CDR (Client Drive Redirection) performance
- Increased CPA (Cloud Pod Architecture) scale up to 250k sessions
- Session “pre-launch”
- Two-Factor Re-Authentication
- Client UI redesign
- vGPU vMotion (came with vSphere 6.7 U1)
- VM hosted apps (published applications from Win10 desktop pools)
- Longer Lived Instant Clones
- Horizon Cloud Services Enhancements & WVD support for Horizon Cloud on Azure
- VMware Skyline Log Assist
- App Volumes 4
- New REST APIs
- Bandwidth savings in Blast (with Blast Codec)
- CPU utilization by Blast has been reduced
- Blast Extreme HEVC High Color Accuracy support
- Automatic codec switching based on screen content
- NSX Advanced Load Balancer (Avi LB) support
As you can see, a lot work has been done and a lot of time has been invested to make Horizon better! These improvements are one of many why I think it’s useless to compare Citrix vs. Horizon, because both can basically do the same if you ask me.
Note: Horizon 8.0 is coming very soon and the beta program for it starts in a few weeks! Stay tuned for more enhancements and innovation. 🙂
Citrix and VMware – Four Options
When I think about Citrix and VMware, there are four options which come up in my mind how a customer could move forward at any given time:
- Replace Citrix with Horizon
- Integrate Citrix with Workspace ONE
- Enhance Citrix with Horizon or Workspace ONE components
- Enhance Citrix with other VMware components
- Use Citrix and VMware Horizon (yes, there are customers with both!)
Replace Citrix with Horizon
The first option is the most obvious one and can happen from time to time due to various reasons. Sometimes the customer is just not happy anymore (technical or commercial) or wants to try something new because of one or more of the other listed options (integration and enhancements in place already).
A migration would be very easy on paper. StoreFront could be replaced by Workspace ONE Access (formerly vIDM), the VDA installed on RDS hosts or virtual desktops need to be replaced with the Horizon agent and on the client side the Citrix Workspace App (Citrix Receiver) gets replaced by a Horizon Client (including HTML5 client).
Caution: Even if it’s technically possible to uninstall Citrix Virtual Desktop Agenda (VDA) and install the Horizon Agent after, this is not something a good consultant would recommend normally. Do it right and rebuild a clean image and test it before going in production.

A replacement could also be done in parallel where you install a Horizon infrastructure beside the current Citrix environment and move the users over whenever you are ready.
If you are running your desktops on Azure together with Citrix Cloud, then the Citrix Cloud piece can be replaced with the Horizon Cloud Service on Azure. Citrix and VMware Horizon are both supported if you are looking for a connection broker for your Windows Virtual Desktops (WVD).
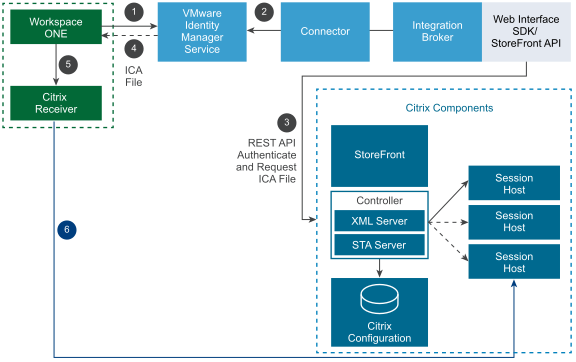
Integrate Citrix with Workspace ONE
The second option doesn’t come up very often. If a Citrix customer is using CVAD only and no Citrix Endpoint Management (formerly known as XenMobile) or Microsoft Intune (or MobileIron) and is considering Workspace ONE for their unified endpoint management of iOS, Android, macOS or Windows 10 clients, then mutual customers could use Workspace ONE (WS1) Access as the web portal or application catalog and single point of access for any application.
As just mentioned already, Workspace ONE users and devices access Citrix-published resources by integrating their Citrix deployment with Workspace ONE Access, which offers an application portal, single-sign on capabilities, conditional access and many other features. Citrix-published resources include applications and desktops from any CVAD infrastructure starting from XenApp 6.0.
All entitlements are still configured in Citrix Studio and you just have to sync these users and groups to the WS1 Access services from Active Directory first.
Beside WS1 Access you need one additional component called the Integration Broker, which can be installed on a Windows Server. The Integration Broker is responsible for the communication with all Citrix farms/sites. The WS1 Access connectors then communicate with the Integration Broker.
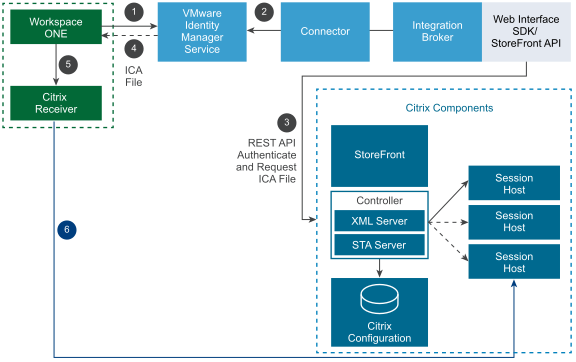
More information can be found here. That’s all what is needed for the integration with Workspace ONE.
Enhance Citrix with Horizon or Workspace ONE components
VMware has customers with a large Citrix footprint of several thousand users. And some of these customers are using Horizon components together with their Citrix infrastructure. The two most used Horizon components in a Citrix infrastructure are:
I am not up to date anymore what Citrix App Layering, Profile Management (UPM) and Workspace Environment Management (WEM) can do for you today. But App Volumes would replace App Layering and Dynamic User Environment (DEM) would replace UPM and WEM in a Citrix environment.
Don’t know if this still is the case, but a few years ago App Layering had very limited features, didn’t perform and the handling of layers was a pain. And WEM just didn’t scale in larger Citrix environment. Probably Citrix UPM still is doing its awesome job but is leveraging FSLogix for profile and O365 container management and I assume that WEM is also installed more nowadays.
If Citrix App Layering is in use, then probably the FSLogix Application Masking feature could be used as well to hide some components in the image, which also allows the admin to manage fewer golden images. This is something you also can do with Dynamic Environment Manager in combination with App Volumes.
Before FSLogix was available to almost every joint Citrix/VMware and Microsoft customer, it totally made sense to use something like DEM for the user environment management, as DEM has similar features as FSLogix.
To understand the integration of FSLogix and AV and DEM better, this article from VMware’s Digital Workspace TechZone is for you.
Maybe you ask yourself now how you could get App Volumes and Dynamic Environment Manager for your Citrix environment? Well, there are a few ways and options:
- Buy the “Horizon Enterprise” or “Horizon Apps Advanced” edition which includes AV and DEM (yes, can happen)
- Buy the “Workspace ONE Enterprise” edition which includes “Horizon Apps Advanced”
- Buy the “Workspace ONE Enterprise for VDI” edition which includes “Horizon Enterprise”
You have to buy another license from another vendor, yes. But, let me explain why this could make sense.
Scenario 1 – Citrix customer is buying Workspace ONE Enterprise
Let’s assume you are a Citrix customer and use CVAD to publish applications to your users, but want to manage your iOS, Android, macOS and Windows 10, IoT devices with one solution or platform. That’s the moment when you go for Workspace ONE as your Unified Endpoint Management (UEM) platform. Here’s what you get with Workspace ONE Enterprise:
- iOS, Android, macOS, Windows 10 and IoT device management (MDM/UEM)
- Workspace ONE Access
- Application delivery and management (mobile and desktop)
- Mobile SSO
- Workspace ONE productivity apps (email, tasks, notes, content/file repository, web, card scanner)
- Multi-Factor Authentication (MFA) with “Workspace ONE Verify” mobile application
- Workspace ONE Intelligence (SaaS-based intelligence and automation engine including reporting)
- Add-on: Remote Management of any device based on Workspace ONE Assist
- Add-on: Workspace Security (Carbon Black offerings)
- Horizon Apps Advanced
The Horizon Apps Advanced edition includes the following:
- RDS published apps (no desktop OS, only server OS) and session-based desktops
- ThinApp (not included with WS1 Enterprise)
- App Volumes
- Dynamic Environment Management
- vSphere Desktop
As you can see, you are removing silos in your digital workspace and can use App Volumes and Dynamic Environment Management at the same time to enhance your Citrix infrastructure.
Scenario 2 – Citrix customer is buying Workspace ONE Enterprise for VDI
The difference between scenario 1 and scenario 2 is the Workspace ONE Enterprise for VDI license, which includes the following components:
- Published desktops and apps (server OS and desktop OS incl. Linux)
- App Volumes
- ThinApp (not included with WS1 Enterprise for VDI)
- Dynamic Environment Management
- vRealize Operations for Horizon (not included with WS1 Enterprise for VDI)
- vSphere Desktop
- vSAN Advanced for Desktop with All-Flash
WS1 Enterprise for VDI makes it possible to have VDI based on the Windows desktop operating system (e.g. Windows 10) as well and adds the infrastructure capability to run your desktop workloads on vSAN enabled clusters! The only thing which differs from the regular standalone Horizon editions, is, that ThinApp and vRealize Operations are not part of the suite. If you have a lot of legacy apps or you need application virtualization or isolation, then take a look at ThinApp.
Applications installers such as MSI files can be packaged into a portable EXE file and can then be run on any physical or virtual Windows PC and delivered with App Volumes (RDS/VDI) or with Workspace ONE (persistent VDI desktop or physical desktop).
And you get the “vSphere for Desktop” edition in both cases which is another killer argument why you could buy Workspace ONE Enterprise (for VDI) licenses as a Citrix customer.
vSphere Desktop
I don’t have any confirmed number, but I assume that 70% of the Citrix customers are using VMware vSphere as their hypervisor. Each regular Horizon edition has vSphere Desktop included which many people are not aware of.
vSphere for Desktop is a special edition, which provides the full range of features of the vSphere Enterprise Plus edition:
- The new image management feature to patch, update or upgrade ESXi clusters (vSphere 7.0)
- vCenter Server profiles and update planner (vSphere 7.0)
- Distributed vSwitch
- Secure access and account management with ADFS (vSphere 7.0)
- Distributed Resource Scheduler (DRS)
- Storage DRS
- Nvidia GRID vGPU
vSphere Desktop is licensed based on the total number of powered-on VMs and has no processor limitation. It’s available in a pack size of 100 desktop VMs with up to 100 users per pack. VERY IMPORTANT: vSphere Desktop can be used for a VDI environment only and a vCenter license is not included in vSphere for Desktop.
This is the only restriction mentioned in the vSphere Desktop FAQ:
vSphere Desktop can be used only to host a desktop
virtualization environment or desktop management and
monitoring tools. Each pack of 100 VMs can be used for
up to 100 users. You can use vSphere Desktop for desktop
management and monitoring tools in a VDI environment
only. Desktop licenses covered by this provision, however,
may not be managed by the same instance of VMware
vCenter that is being used to manage non-desktop
OS virtual machines.
So, what is considered as a “desktop virtualization environment” including monitoring tools? Normally you would separate your Citrix or Horizon infrastructure servers from the virtual machines which provide the virtual desktops and applications. But this design is more a leading practice and recommended by reference architectures and therefore it is technically possible to mix the RDS and VDI virtual machines with the infrastructure servers like:
- Connection Server / Delivery Controller
- Workspace ONE Access / StoreFront
- Unified Access Gateway / NetScaler
- Active Directory
- Monitoring Tools (vRealize Operations / Director)
- any “other infrastructure directly related to and exclusive to the VDI environment”
In a Citrix Virtual Apps and Desktop environment you can use vSphere Desktop to provide the virtual machines (desktops) and the underlying infrastructure. In this use case, you are licensed per virtual machine and virtual machines used to host the infrastructure servers. These two numbers will be counted against your “total powered-on VM” count. If your Citrix environment has a 100-pack of vSphere Desktop licenses and you host 85 VDI desktops and 15 VMs that host the Citrix VDI environment, then you have used up all the 100 vSphere Desktop licenses.
vSAN Advanced for Desktop
vSAN Advanced for Desktop is shipped together with Horizon Advanced, Horizon Enterprise and Workspace ONE Enterprise for VDI. This license is available for customers using vSAN exclusively for a VDI infrastructure.
Horizon Universal License
The Horizon Universal License is a single subscription-based license, which is included in the Workspace ONE Enterprise edition and serves as an entitlement for all Horizon products, namely Horizon Cloud (including Horizon Cloud Apps) and Horizon on-premises (including Horizon Apps). Thus, the universal license entitles you for the following solutions:
This universal license gives customers the choice to start with an on-premises Horizon deployment and to move to the cloud (or vice versa) without requiring a new license.
Note: Because it’s the universal license and not a regular Horizon license, which is included in the WS1 editions, vRealize Operations (vROps) is not part of this subscription bundle. If needed, vROps can be bought as a standalone license.
Thin Client Management
I thought it is worth mention it here. Keep in mind that you could use a platform like Workspace ONE to manage your thin clients. If your environment is heavily using thin clients you could “build” your own thin client based on Windows 10 IoT Enterprise and manage it via Workspace ONE.
E.g. Workspace ONE can manage Dell Wyse 5070 thin clients with Windows 10 IoT Enterprise. If needed, WS1 can configure the Unified Write Filter (UWF) feature to protect your thin client drives for any changes (saved data, setting changes or app installations). This is also helpful for increasing security for kiosk PCs in hotels, public spots, internet cafés etc. or for devices where it’s not expected to have new application frequently added.

Enhance Citrix with other VMware components
We know that you could make your Citrix environment “better” with Horizon components like App Volumes or Dynamic Environment Manager and vSphere components like vSphere and vSAN. But there are other products and components which could make sense in a Citrix environment.
I believe, today, VMware has something which you could call a partnership and both CTOs are clearly leading the way:

I don’t know if it ever happened before that Citrix mentioned VMware on stage at Synergy, but the announcement from the above picture brings me to my first solution which you could use for your Citrix deployment.
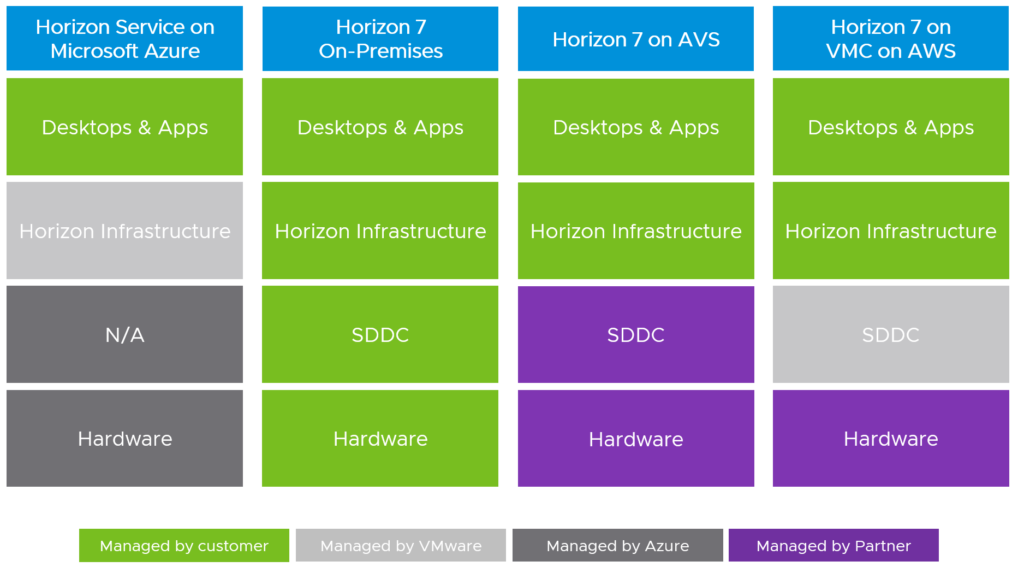
VMware Cloud on AWS
What has been announced at Citrix Synergy 2019? The intent to officially support CVAD running on VMware-based clouds, starting with VMware Cloud on AWS. Many organizations are evaluating or even using a hybrid cloud approach already. This announcement should help Citrix customers, who are running their workloads on vSphere already, to seamlessly move to the cloud to experience a consistent infrastructure with consistent operations.
Because you are using the same technology stack on-prem and in the cloud, this allows you to easily bring your RDS and VDI golden images to the cloud without any a conversion.
I see two deployments options here. Either you leverage the Citrix Cloud services (use VMC as a resource location) or manually install your Citrix infrastructure like you would normally do in your on-premises environment.

Note: VMC on AWS is citrix-ready since Q4 2018!

If you would like to know more about running Citrix Virtual Apps and Desktops with VMC on AWS, please watch the VMworld 2019 recording of the session “Building Global Citrix Virtual Apps and Desktops with VMware Cloud on AWS (HBI2247BU)“. There’s also a recording of the US 2019 session “Building Global Citrix Virtual Apps and Desktops with VMware Cloud on AWS“, presented by Andrew Morgan and James Hsu.
Interesting facts:
- It takes about 60-70min in average to deploy a new SDDC on VMC on AWS
- 12min is the average time to add a new host
- Stretched clusters give you a guaranteed SLA of 99.99%
- Sync your VM templates with your Content Library
- Andrew and James deployed 100 Win10 desktops in 5min only
- PVS and MCS both work on VMC on AWS
NSX – Software-Defined Networking
Digital transformations are nothing new, but get more complex with newer technologies we have today. One very important topic which came up in 2019 and is one of the most important trends for 2020 is “cyber security” or “zero trust security”. VMware and Citrix are both pointing to a zero trust approach to protect the workforce, any app and data. VMware has defined 5 pillars of zero trust for a digital workspace and “transport/session trust” is one of them with these parameters:
- Micro-Segmentation
- Transport Encryption
- Session Protection
For secure transport of a user’s session you would use appliances like the Unified Access Gateway (UAG) or Citrix NetScaler. To achieve a trusted network access within the data center and between workloads, you’ll need something like NSX and micro-segmentation. Citrix has only a SD-WAN solution to protect branch offices and branch users, but no solution for micro-segmentation. What is micro-segmentation and why is it important?
Imagine that network policies can be bound to a virtual machine or in our case to a virtual desktop and dynamically follow a virtual desktop. This is very helpful in the case of VMC on AWS for example. You can easily move the workload to the cloud and move the networking policies together with the VM, because the underlying stack on VMC on AWS (based on VMware Cloud Foundation) includes NSX and the vSphere hypervisor.
How would you secure the communication and access between desktops in the same VLAN? All desktops on a VLAN can communicate freely and one compromised desktop allows lateral movement. With NSX we can provide granular control of desktops and user/group based access control. This is micro-segmentation.

Here are two articles about Citrix and NSX from VMware and Citrix:
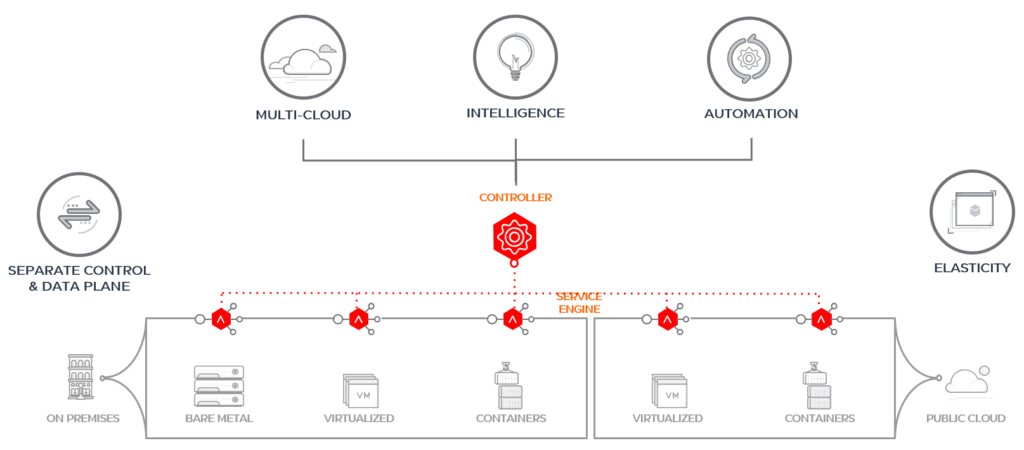
If you are interested in 100% software-defined networking and are thinking to replace an existing hardware or virtual ADCs (application delivery controllers), take a look at NSX Advanced Load Balancer (formerly Load Balancer from Avi Networks).
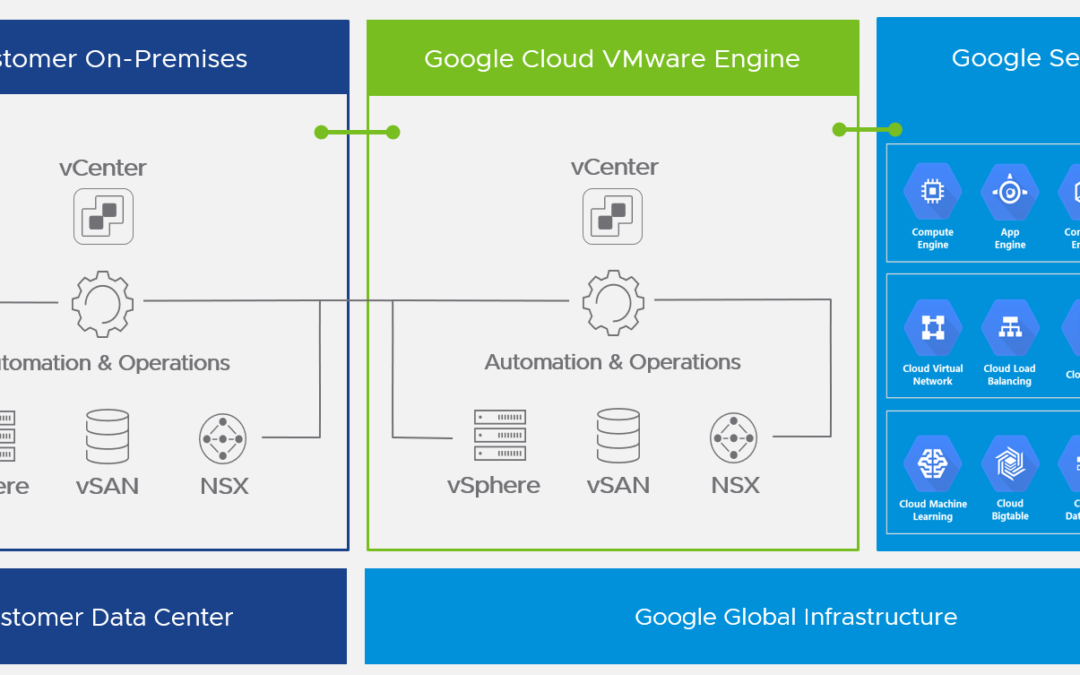
Where VMware Horizon differs from Citrix
Now you know the four options you have as a Citrix customer when considering VMware products for your current and future environment. Let me explain you why you shouldn’t compare Citrix and VMware Horizon anymore. To get started, you need to understand all the different options you have and how and where you could consume VMware Horizon:
- Horizon on-premises
- Horizon Cloud
- Horizon DaaS
And with the different desktop virtualization offerings there are also different management responsibilities for the customer, partner and VMware:
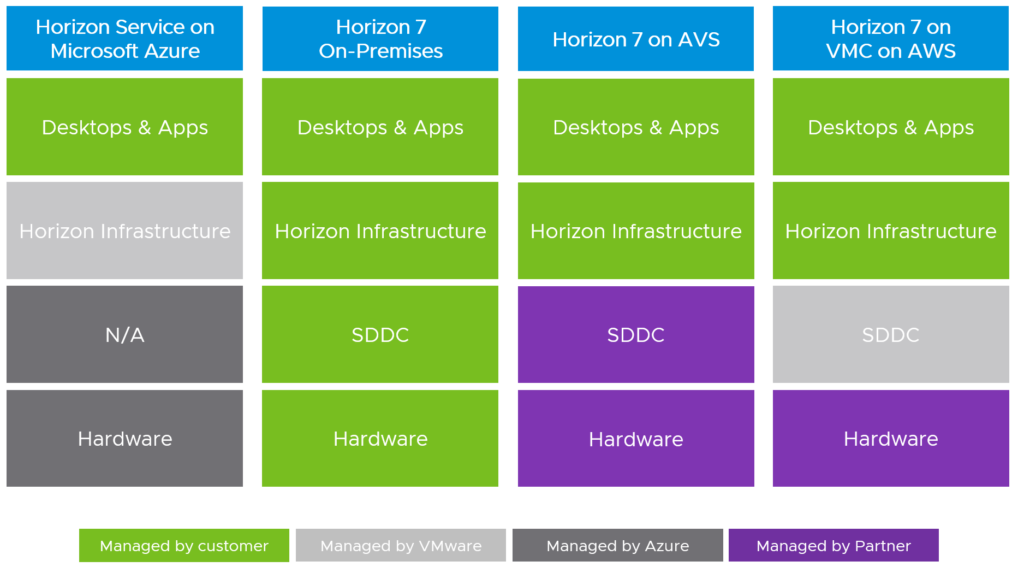
Customers have the flexibility to choose the level of control they want to have over the Horizon and data center infrastructure. If full control of the solution is needed, then you would probably implement Horizon with vSphere on-premises. For use cases where you only would like to maintain the desktop and apps only without concerning yourself about managing any infrastructure, Horizon Cloud on Azure could be one option.
Horizon On-Premises
The biggest difference for me, if you really want to compare Citrix and VMware in a better way, is to see the big picture. People need to understand that it is totally normal that one vendor sometimes is ahead or behind the competitor. The feature set from both vendors, only considering desktop virtualization, is pretty much the same.
When you start a desktop virtualization project and design the solution, you also have to think about the data center part. I’m am not only talking about Horizon and the storage or network requirements here. It’s important to understand the general strategy and vision of VMware and your employer/customer.
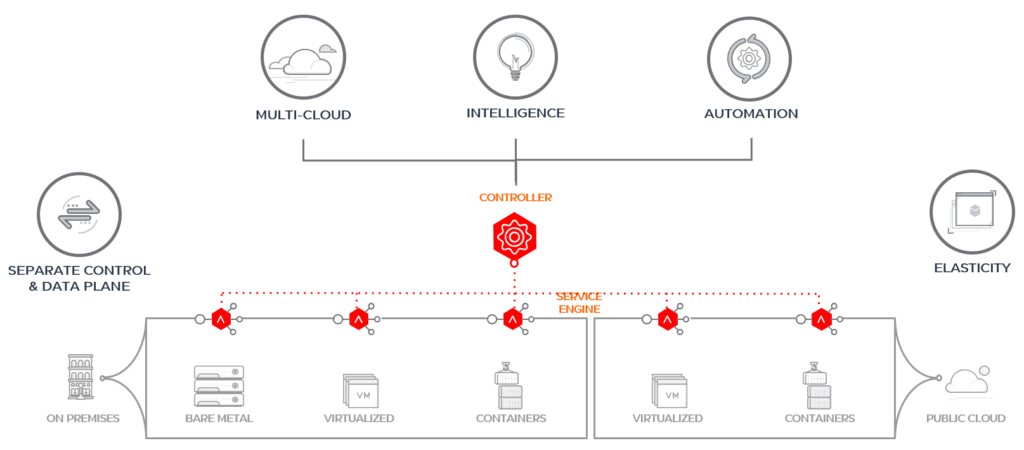
Today, automation is a design requirement and you ideally build your on-premises infrastructure based on public cloud principles. Companies don’t start anymore by buying hardware and think about automation later. They want to buy and build something that can be automated from day 1 like it’s done in the public cloud. Everything needs to be agile and elastic and should be able to change when any kind of change occurs.
Because of that it is essential to understand the cloud infrastructure part very well and this is the big difference between Citrix and VMware. We shouldn’t only talk about EUC (End-User Computing) only, but even consider other projects or domains of the infrastructure:
- Does it fit in my cloud operating model?
- Can I use an existing solution to automate it (software and hardware)?
- How would I move my workloads to the cloud tomorrow?
- Can I integrate existing solutions in my ecosystem (e.g. security, IPAM etc.)?
- Can it be integrated in our existing or new platform for modern applications based on containers?
- What about day 2 operations if I need to expand?
- Can I reduce my silos and reduce the number of vendors and licenses somehow?
The installation of a complete Horizon (or Citrix) infrastructure can be done in a few days, normally, but larger environments require a lot of automation and integrations into the existing infrastructure. Then we talk about several months and not days or weeks anymore.
Horizon on VMware Cloud Foundation
VMware Cloud Foundation (VCF) is made for any workload and is a hybrid cloud platform which provides a set of software-defined components for compute, storage, networking, security and cloud management. VCF is an engineered solution that integrates the entire VMware stack without the need you dealing with complex interoperability matrixes.

The architecture is built on VMware’s Validated Designs (VVD) to reduce the risk of misconfigurations or design failures. The VCF stack is also used with VMC on AWS or Azure VMware Solutions (AVS) for example. This is another reason that clearly shows that this technology stack is the right for any (VMware) infrastructure. If workload mobility is part of your IT strategy, then only VMware can offer this at the moment.

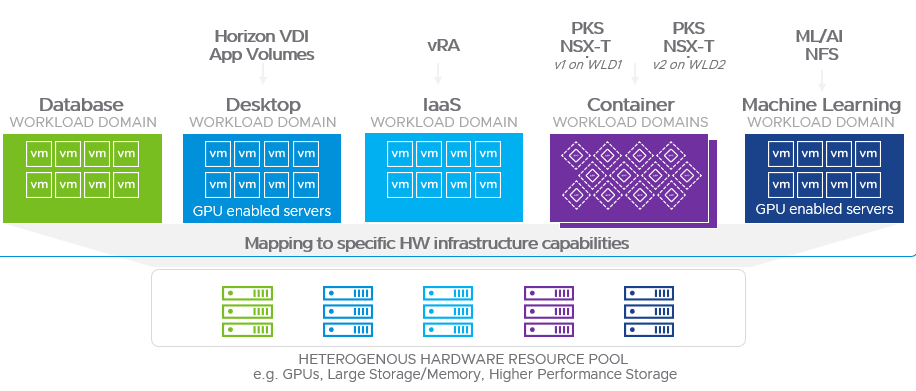
VMware Cloud Foundation has a “siloed” approach when it comes to the deployment. Based on different hardware resource pools you can create different so-called workload domains (WLD). Each WLD is a different SDDC instance which is managed by software-defined policies. The Horizon deployment can form one or more VDI WLDs.
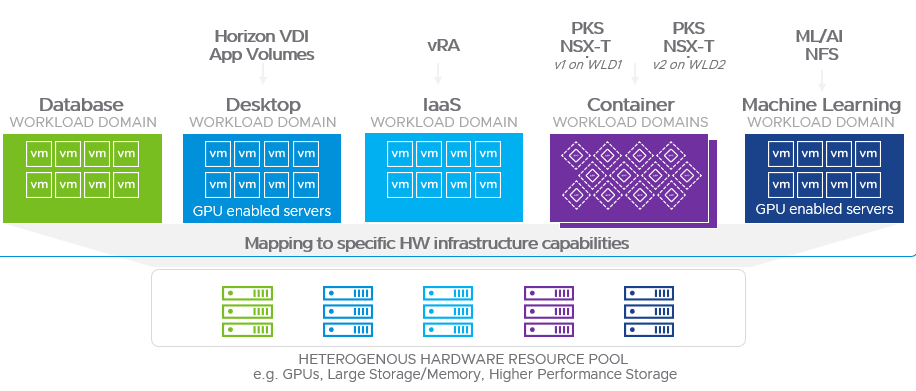
Because it’s a standardized approach, VCF makes it very easy to scale on-demand depending on your needs. To get started you’ll need a management workload domain, which is a special-purpose workload domain dedicated for infrastructure and management components like the SDDC Manager, vCenter Servers, vRealize Suite and NSX. The SDDC Manager is responsible for the creation, update or deletion of a workload domain.
Using the regular standard architecture model for VCF, an environment starts with at least 4 physical servers for the management domain, 3 servers for the VI workload domain (Active Directory, SQL servers, any general infrastructure VM) and 3 servers for a Horizon VDI workload domain. This gives us a starting point of 10 physical servers if you build a complete IT infrastructure from scratch. Otherwise you just need the management domain and VDI workload domain with a total minimum of 7 physical servers.
There is also the option available of a consolidated architecture design for smaller environments. In this design the management and workloads run together on a shared management domain. But the consolidated architecture doesn’t support the automated deployment of Horizon yet.
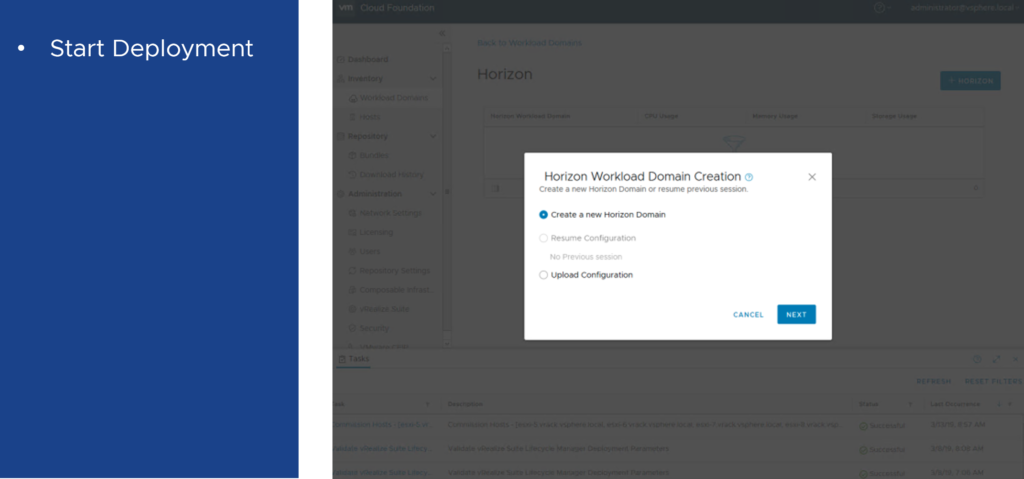
For the automated deployment of Horizon on VCF you would use the SDDC Manager to deploy Connection Servers, App Volumes, Dynamic Environment Manager and Unified Access Gateways. Let me show you some part of the wizard to create a VDI WLD:
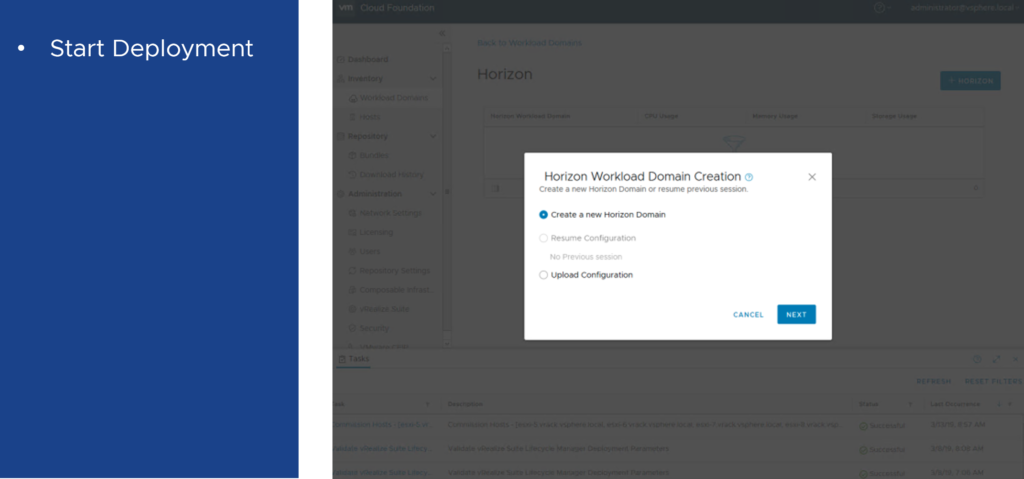
You don’t have to install the components by hand, but still need to do your homework before you can deploy the WLD.

I skipped a few steps. You need to upload the Windows server template, convert an existing VI WLD to a Horizon VDI WLD, configure the Horizon AD service account, provide a SQL server and provide information for the load balancers before you reach the step where you enter the details for the connection servers:

One more App Volumes Manager can be added as well:

If you reached the end, you’ll see a review page to do a final check and after that you can run a validation of all your inputs. The deployment of at least one Connection Server is required, but Horizon Composer Servers, UAGs, App Volumes and DEM are optional components and could be skipped.
To expand a current VDI WLD to install UAGs or just to expand the Horizon Pod (add ESXi hosts or Connection Servers) VCF gives you the option to start small and expand later. In the future it should also be possible to shrink a VDI WLD.

The lifecycle management with VCF is very easy. Available updates for all components are tested for interoperability and then bundled with the necessary logic for the proper installation order. VCF offers automated lifecycle management on a per-cluster basis (one WLD can have one or more clusters). This allows admin to target specific workloads or environments for updates independently of the rest of the environment.

For a VDI workload domain VCF delivers a nice view to see the allocated servers/resources and each component related to this workload domain.

Horizon on VCF on VxRail
So, we know now that VMware Cloud Foundation is the “easy button” for the deployment of the full vSphere stack including vSAN, NSX, vRealize Operations, vRealize Automation, vRealize Log Insight and so on. VCF on VxRail goes one step further and provides you the “one-click upgrade button” for your vSphere stack including the server hardware and firmware. VxRail bundles are pre-configured and pre-tested and therefore validated by Dell EMC and VMware.

The cool thing with VxRail is, that it gives you flexibility for your workloads and that you can choose between different series based on Dell EMC PowerEdge servers. You have multiple compute, memory, storage, network and graphics (M10, P40, T4) options available to cover your workloads and applications with the right server specifications.

Citrix (on VCF) on VxRail
Since VxRail is an HCI appliance, it can run everything on top. I know some larger Citrix customers who are running their Citrix infrastructure on VxRail. It is also possible to run your Citrix infrastructure on VCF on VxRail on a VI workload domain. The only difference with Horizon is the missing automation and integration into the whole (VCF) stack.
Intrinsic Security
In case you missed it, VMware bought Carbon Black and has a new security business unit now. And this is one very important differentiator in this virtual cloud computing space. If VMware’s software-defined data center is your platform of choice already, it makes sense to use a security solution which can be fully integrated and provided by the same vendor.

Imagine, that the endpoint protection agent is already integrated in the Horizon Agent and that you could deliver security from your mobile endpoints (Windows, Mac, Linux) to your workloads (VMs or container) in your data center or any cloud (AWS, Azure, GCP). Sounds too good to be true? No, this where the VMware products are heading, especially with Workspace ONE and Horizon (next-gen AV, behavioral EDR, audit and remediation)!
Workspace ONE for Horizon
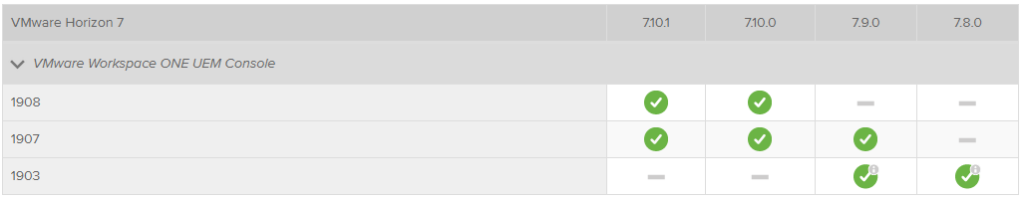
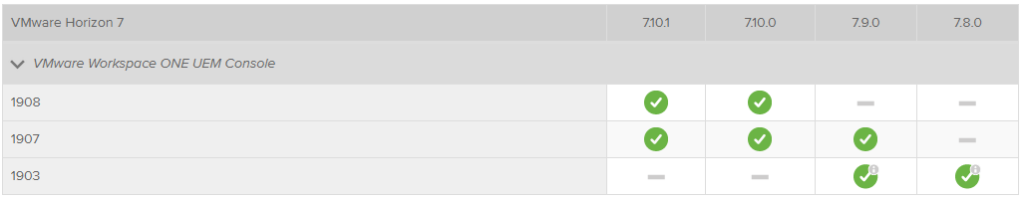
I mentioned it already, Horizon is included in the Workspace ONE Enterprise editions. I haven’t covered the case yet where you could combine Horizon and Workspace ONE. If you provide your users persistent virtual desktops based on Windows 10, then it is also possible to manage those with Workspace ONE as well. This will help if you want to move away from a traditional PC lifecycle management (PCLM) solution and move to a modern management approach. So far this only supported with Horizon on-premises installation. Take a look at the product interoperability matrix:
For which other use cases could this be useful?
- Physical desktops with Horizon Agent installed (Remote PC access)
- Physical servers with Windows 10 installed (e.g. HP Moonshot)
I don’t know if the last option has been tested but Windows 10 is a supported operating system for HP Moonshot cartridges.
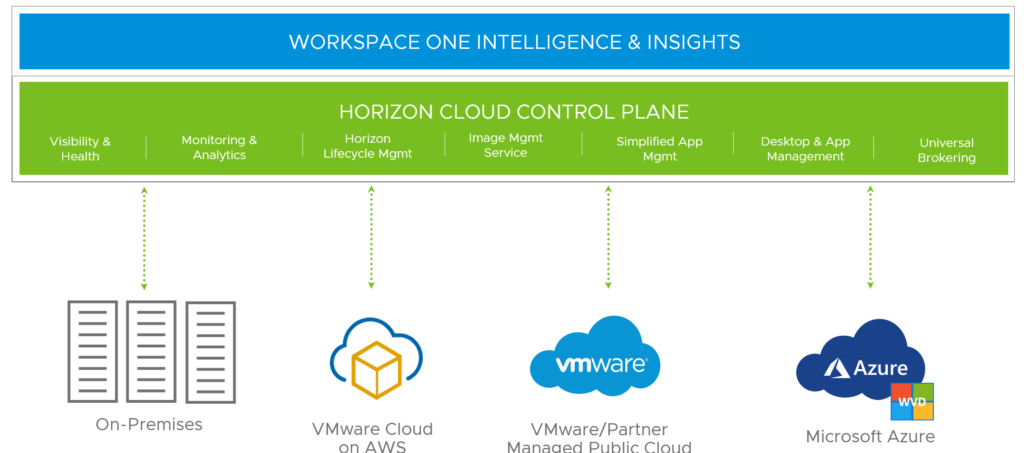
Horizon Cloud
The Horizon (Cloud) Service is a group of cloud-based services that deliver features for Horizon deployments. This includes the Windows Virtual Desktop (WVD) on Azure as well since the 17th March 2020. Any customer who is using a Horizon subscription license, such as the universal license, can use the Horizon Service.
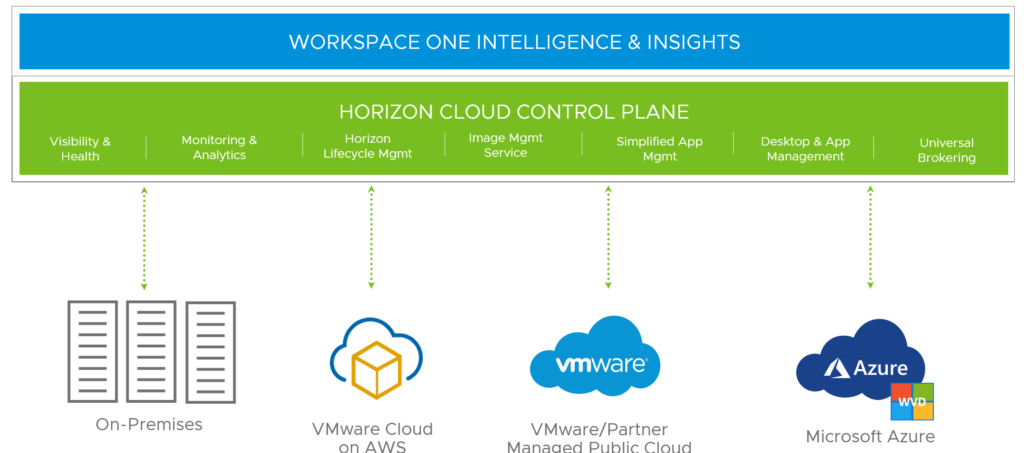
The goal of Horizon Cloud is to provide a single-pane management UI for the delivery and management of your desktops and applications. This is the overview dashboard which shows some information about the health and capacity of all your Horizon deployments.

The Cloud Monitoring Service (CMS), which is one of the central services of the Horizon Service, provides data about the user’s session and issues. It can show you how many users and their user experience are impacted related to issues (latency, protocol, slow logon).
In the administration console you can configure the role-based access (RBAC) for your helpdesk admins. It allows them to log in to the admin console and use the search feature to look up users. The help desk administrator can then look up the user’s sessions and perform troubleshooting or desktop maintenance operations.

The Image Management Service (IMS) is one of the coolest feature of the Horizon Service. As the name suggests it already, it allows you to manage Horizon images from the cloud. You can create, customize, publish and even version all your different images for your Horizon pods. IMS provides a centralized catalog for your images and these can be automatically replicated across the cloud-connected Horizon pods.
Important note: The current release of Horizon Cloud only supports Windows operating systems and on-premises Horizon pods.

Universal Broker
When I joined VMware in May 2018 I was waiting for a feature like this and tried to explain some product managers (PM) that we need something like the Universal Broker. I was looking for a solution that we can avoid E/W traffic in a Horizon multi-pod deployment. I think I tried to explain it to some of our PMs using Citrix’ Optimal Gateway Routing for
Storefront & NetScaler capability. Nobody understood me, but at least we have it now. 😀

Horizon Universal Broker is the cloud-based brokering technology used to manage and allocate virtual resources from multi-cloud assignments to your end users.
These are the listed key features in the VMware Horizon Cloud Service documentation:
- Single FQDN for all multi-cloud assignments
- Global pod connectivity and awareness for optimal performance (no longer need for GSLB and no more E/W traffic)
- Smart brokering (awareness of geographical sites and pod topology)
This diagram shows the Universal Broker components and how the traffic flow works:

- From Horizon Client, the end user requests a virtual desktop by connecting to the Horizon Universal Broker service through the brokering FQDN. The service uses the XML-API protocol to authenticate the Horizon Client user and manage the connection session.
- After determining that Pod 1 in Site 1 is the best available source for the desktop, the Horizon Universal Broker service sends a message to the Horizon Universal Broker client, which runs on the Horizon 7 Cloud Connector paired with Pod 1.
- The Horizon Universal Broker client forwards the message to the Horizon Universal Broker plugin, which runs on one of the Connection Server instances within Pod 1.
- The Horizon Universal Broker plugin identifies the best available desktop to deliver to the end user.
- The Horizon Universal Broker service returns a response to Horizon Client which includes the unique FQDN of Pod 1 (typically the FQDN of the Pod 1 load balancer). Horizon Client establishes a connection with the load balancer to request a protocol session with the desktop.
- After passing through the local load balancer, the request goes to the Unified Access Gateway for Pod 1. The Unified Access Gateway validates that the request is trusted and prepares the Blast Secure Gateway, PCoIP Secure Gateway, and tunnel server.
- The Horizon Client user receives the specified desktop and establishes a session based on the configured secondary protocol (Blast Extreme or PCoIP).
Horizon DaaS
In 2013 VMware acquired Desktone. A company that was specialized in delivering desktops and applications as a cloud service. The product got renamed during the years and kept the name “Horizon DaaS“. This is the reason that Horizon DaaS is not just another version of the classic “Horizon” or “Horizon View” since it was a different product which VMware bought. It’s important to know that there are technical differences/characteristics between Horizon and Horizon DaaS because of this history.
Horizon DaaS is the Horizon Desktop-as-a-Service platform for service providers. Not many people understand and know this specific product and you won’t find a lot of content on blogs about it.
The most recent information, beside the official Horizon DaaS documentation, can now be found here 😉 or on Johan’s blog, where he published a lightboard series about Horizon DaaS.
As a service provider you have different options to provide a “managed desktop” or “DaaS” offering:
- Dedicated Horizon deployment hosted in your data center (licenses through VCPP rental)
- Horizon Cloud Service (DaaS offering licensed through VCPP MSP)
- Horizon DaaS – multi-tenant Horizon deployment hosted in your data center (VCPP rental)
Again, Horizon DaaS should be seen as something different than Horizon, it’s really just not Horizon. But the future strategy and look of the user interface will be aligned with Horizon Cloud, because VMware’s Horizon Cloud Service is powered by Horizon DaaS already.
If multi-tenancy is a key requirement for your business, you’ll have to go with Horizon DaaS. Otherwise the regular Horizon edition or the combination with Horizon Cloud are the right fit. Horizon DaaS and Horizon have common components like vCenter, Agents, UAGs etc., but there are also different appliances with Horizon DaaS which replace components of a regular Horizon deployment.

With Horizon DaaS you are going to have “Service Provider” appliances, “Tenant” appliances and “Tenant Resource Manager” appliances, which form the DaaS back-end.
The Service Provider Appliance is the first appliance installed in a data center and provides the foundation to install the remainder of the Horizon DaaS application.
The Resource Manager abstracts the specifics about the desktop infrastructure from the tenant appliances and allows multiple Desktop Managers to communicate with their respective virtualization resources. A Resource Manager appliance integrates with the hypervisor and storage infrastructure in a given data center. A single Resource Manager appliance can be shared across multiple tenants.
The Tenant Appliance provides the tenant with both end user and administrative access to their virtual desktops. End users access and manage their individual virtual desktops via the Desktop Portal. Administrators create and manage their virtual desktops via the Enterprise Center. The Tenant Appliance includes the Desktop Manager, a per-tenant resource that manages each tenant’s virtualization resources and communicates with a tenant’s hosts (hypervisors). You associate the desktop manager with a resource manager and one or more host managers.
It’s not 100% clear from the Horizon DaaS 8.0.0 Service Center guide, but a Tenant Appliance replaces the Connection Server you would know from a regular Horizon deployment (one of the differences I was already referring to).
Use what makes sense
For me it is very important that you understand how VMware products can help and that people are aware of all the different options they would have with VMware and Horizon.
You must form your own view and opinion and I hope this article was useful to get facts from both worlds (based on my best knowledge and experience). If you understand Horizon better now, this is already fine for me.
There was no intention to lead the path to a way where you would replace Citrix. The new information should help you to make the right decision for your company, your environment, your needs and use cases. Use the products which make sense for you and make sure you understood all options.