
VMware vSphere Foundation and VMware Cloud Foundation Overview
As some of you already know, VMware by Broadcom is moving forward to primary offers only: VMware vSphere Foundation (VVF) and VMware Cloud Foundation (VCF). If you have missed this announcement, have a look at my blog A New Era: Broadcom’s Streamlined Approach to VMware’s Product Lineup and Licensing.
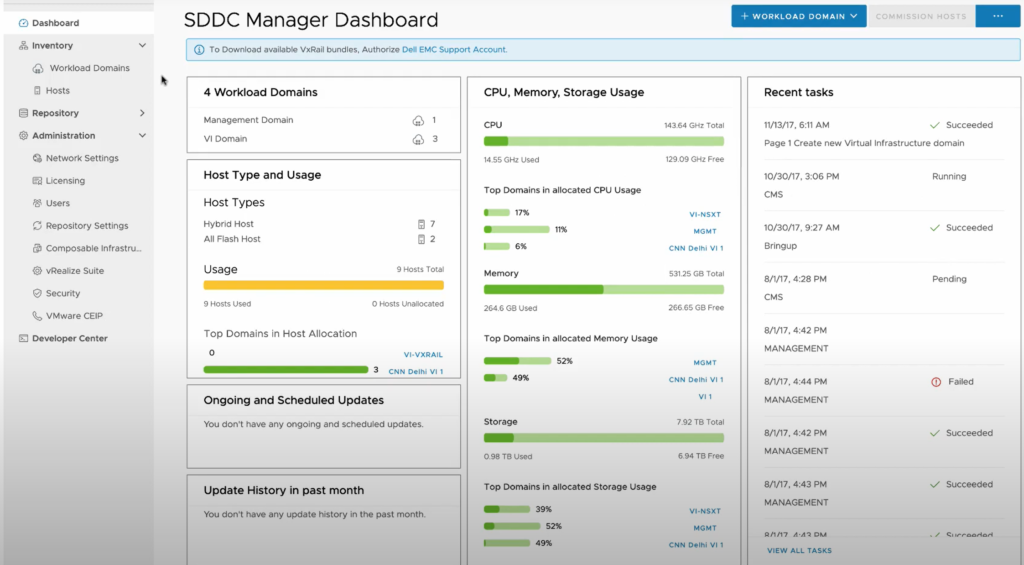
Since a lot of solutions and different editions from before are included, I thought it might be helpful to summarize in a little bit more detail what is known to partners, analysts, and some customers already. I am also adding some screenshots from VMware websites and presentations, which should help everyone get a better understanding of VVF and VCF.
vSphere Foundation and VMware Cloud Foundation
I have included the vSphere editions for smaller use cases and projects as well.
Please note that ROBO licenses are not available anymore and I expect the edge division at VMware by Broadcom to come up with additional bundles in the future.
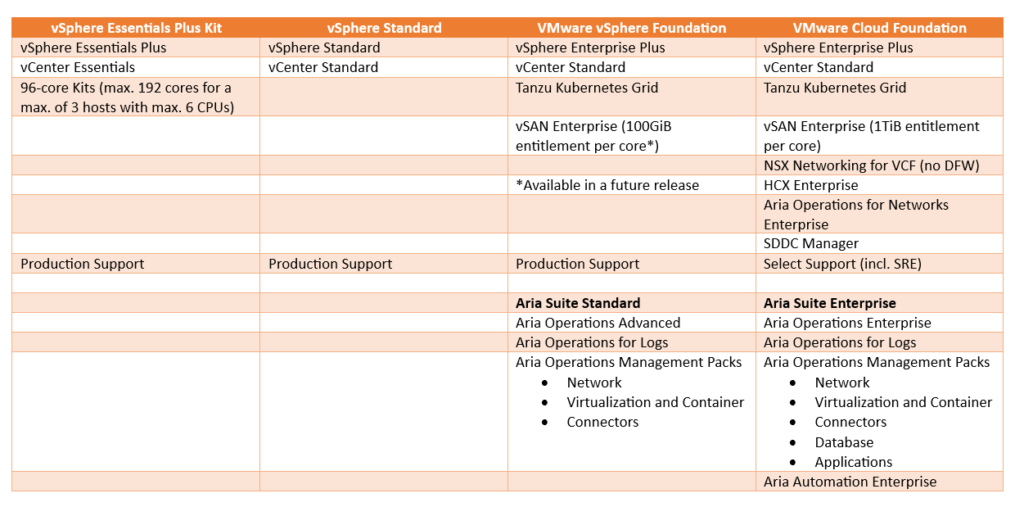
More details about the different products and the features included in the Aria suites can be found here: VMware Aria Suite Editions and Products
If you are looking for more information about the Aria Operations management packs (formerly known as True Visibility Suite or Aria Operations for Integrations), have a look here: VMware Aria Operations for Integrations Documentation
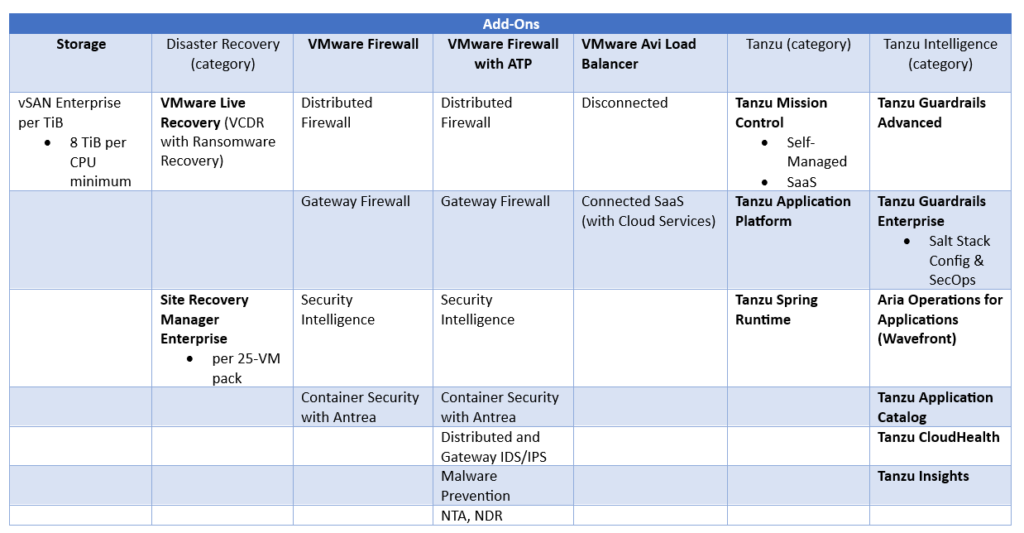
Add-ons for VVF and VCF
The table below gives you an overview of which add-ons are available at the time of writing this blog.
Make sure to contact your VMware representative to understand which add-ons are available for VVF and VCF.
Note: Available add-ons are the text in bold.
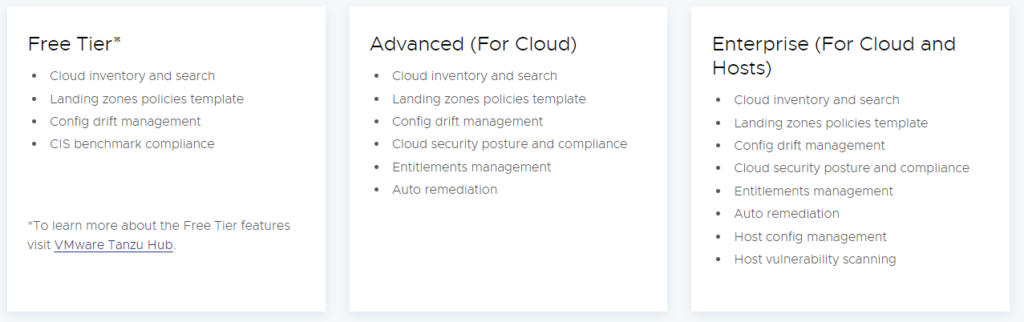
Tanzu Guardrails (formerly VMware Aria Guardrails)
Looking at the official Tanzu Guardrails product website we can learn the following:
Note: It seems that Tanzu Hub is part of Tanzu Guardrails Advanced and Enterprise
SRE Services for VMware Cloud Foundation
VMware Site Reliability Engineering (SRE) Services for VMware Cloud Foundation provide VMware expertise to create highly reliable and scalable cloud environments. The services provide a range of capabilities from patching and upgrades to security hardening to automated management and operations.
The SRE Services for VCF datasheet can be found here.
How to count cores for VVF/VCF and TiBs for vSAN add-on?
Please have a look at this updated knowledgebase article: KB95927
What about VMwara Aria SaaS?
Customers have no more option to buy VMware Aria products as standalone products or as SaaS: https://blogs.vmware.com/management/2024/01/dramatic-simplification-of-vmware-aria-as-part-of-vmware-cloud-foundation.html
The Aria cloud management capabilities are available only as components of VMware vSphere Foundation and VMware Cloud Foundation, which are sold for deployment on-premises or on certain public cloud providers including VMware Cloud on AWS. Existing Aria SaaS subscriptions will continue through the end of their term. At time of renewal, customers should purchase VMware vSphere Foundation and VMware Cloud Foundation.
Use this KB96168 to understand which products are impacted by this new policy.
What about Tanzu products?
For some of us, it seems that the Tanzu products are only available as VVF/VCF add-ons, which is not true.
Based on the different comments on various social media platforms and the interviews we have seen from VMware by Broadcom executives, we can say the following:
- vSphere with Tanzu (aka TKGs) with its Supervisor architecture is going to be the long-term strategy (part of VVF and VCF)
- Heavy focus on Tanzu Application Platform (TAP) and Tanzu For Kubernetes Operations (TKO)
- We can expect continued support for TKGm and TKGi
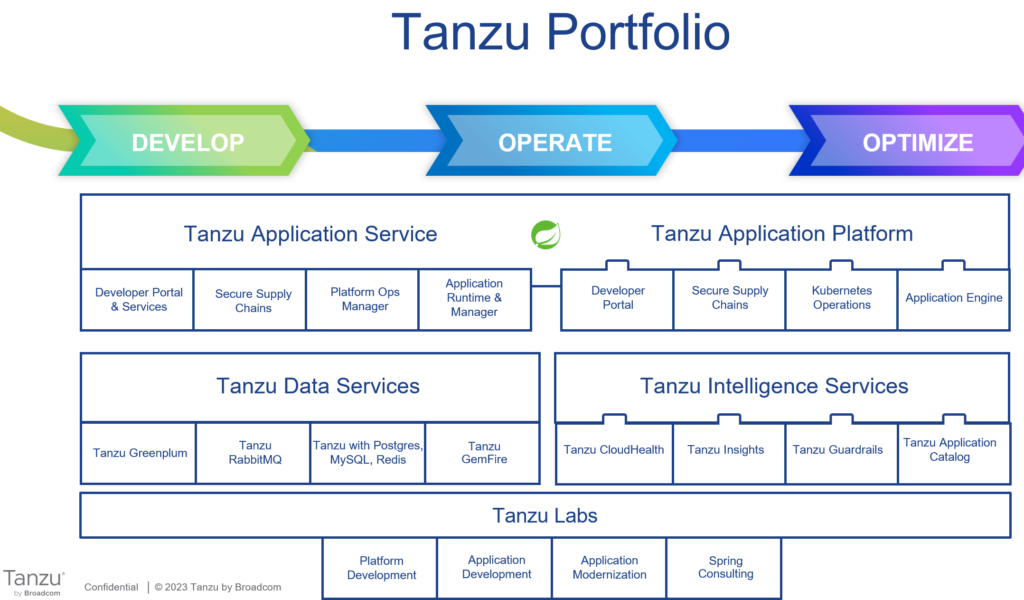
Tanzu Portofolio and Strategy Recap
At VMware Explore 2023, VMware presented the “develop, operate, optimize” approach when they talk about platform engineering:
- Develop – Secure paths to production
- Operate – Deploy, managed and scale applications seamlessly
- Optimize – Continuously tune cost, performance and security of applications at runtime
We learned that VMware (by Broadcom) is going to invest in TAP, Spring, TKO and data services. What’s the difference between TAS and TAP again?
- Tanzu Application Service – Opinionated platform built on Cloud Foundry
- Tanzu Application Platform – Modular and portable PaaS for any conformant Kubernetes
Tanzu for Kubernetes Operations Refresher
TKO comes in two different editions:
- Tanzu for Kubernetes Operations Foundation (TKO-F)
- Tanzu Mission Control (includes TMC self-managed)
- Tanzu Service Mesh
- Tanzu for Kubernetes Operations (TKO)
- Tanzu Mission Control (includes TMC self-managed)
- Tanzu Service Mesh
- Tanzu Observability (aka Aria Operations for Apps, formerly Wavefront)
- Antrea (CNI)
- TKGm
- Harbor, HA Proxy, Calico, FluentBit, Contour, Prometheus, Grafana
- Avi Essentials (NSX ALB)
Note: NSX Advanced Load Balancer (aka NSX ALB) is no longer part of TKO since NSX ALB can be purchased as an add-on
Last Comments
While I was waiting to publish this blog, William Lam wrote a more detailed blog about VMware vSphere Foundation and VMware Cloud Foundation as well.
It is still early days and we can expect more updates from VMware by Broadcom soon. 🙂



















 The Future
The Future





























