Workspace ONE Mobile Threat Defense
It has been a while since I wrote about end-user computing (EUC) or anywhere workspace related topics, but I was waiting for a solution like this when I joined VMware back in 2018 as a EUC Solution Architect focusing on Horizon and Workspace ONE. Before I left for vacation in mid-June, VMware announced the general availability of Workspace ONE Mobile Threat Defense (MTD), which brings mobile security integrated directly into Workspace ONE Intelligent Hub.

Workspace ONE (WS1) is VMware’s digital workspace platform that enables companies to simply and securely deliver and manage any app on any device. It integrates access control, application management and multi-platform endpoint management and is available on-premises deployment or as a cloud service (SaaS).
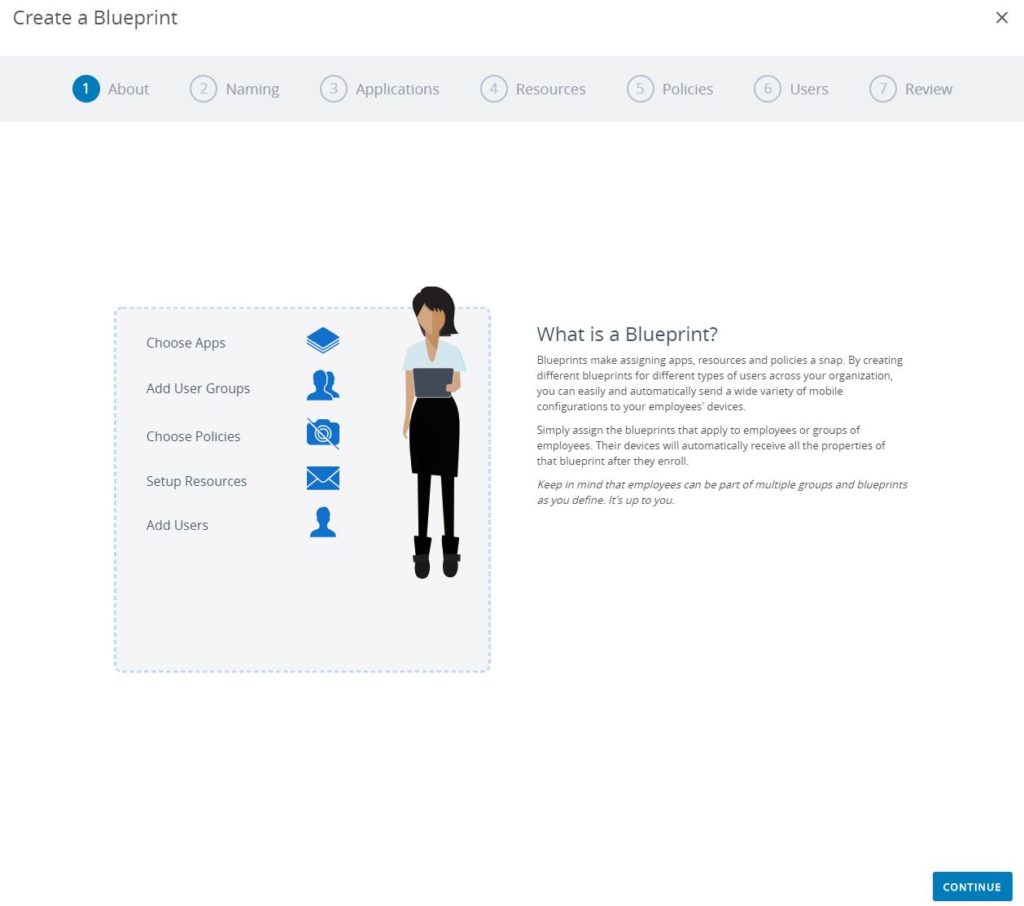
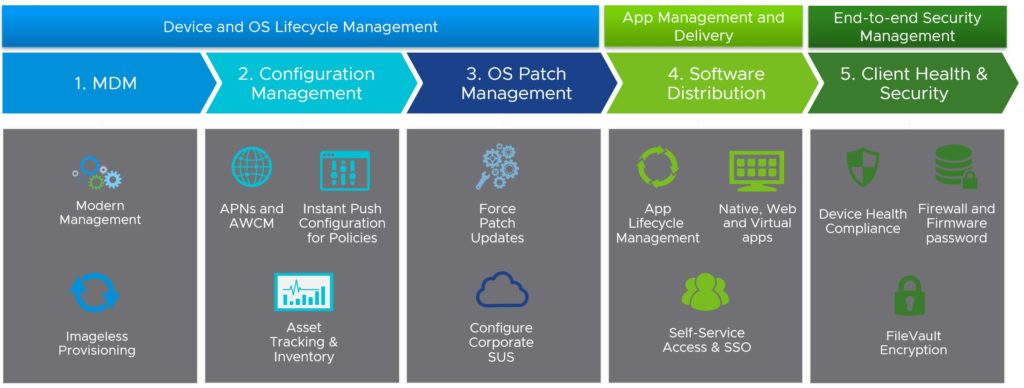
Part of WS1 is Workspace ONE UEM (Unified Endpoint Management), which gives customers the capabilities to manage the full lifecycle of any endpoint – mobile (iOS, Android), desktop (Windows 10/11, macOS, Chrome OS, Linux), rugged devices and even IoT devices – in one single solution and management console.
While Workspace ONE can enable a full zero trust architecture and provides different components that make a digital workspace more secure, there was no integrated solution available for mobile devices.
Before this announcement back in June 2022, Workspace ONE customers had to use Workspace ONE Intelligence with Workspace ONE Trust Network that integrates threat data from 3rd party vendors that provide EDR (endpoint detection and response) solutions, mobile threat defense capabilities, or cloud access security brokers (CASB). WS1 Intelligence provides users and admins insights into the risks of devices and users.
Workspace ONE Intelligence provides visibility by aggregating data from multiple sources with the goal in mind to better understand the security posture of a user’s device and employee experience. In the case of mobile security, by using Workspace ONE Trust Network, admins can integrate and aggregate threat data from external sources like Zimperium Mobile Threat Defense, Netskope or Lookout Mobile Endpoint Security.
Mobile Endpoint Security
The next step in the evolution is a WS1 UEM-integrated mobile protection powered by Lookout. Finally, customers can provide mobile specific protection and not only identity or network-based security mechanisms.
What started with an API integrated approach with Workspace ONE Trust Network has become one solution by integrating Lookout’s SDK (Software Development Kit) into Workspace ONE’s Intelligent Hub. Customers do not have to install or activate a separate app.
Workspace ONE Mobile Threat Defense Key Features
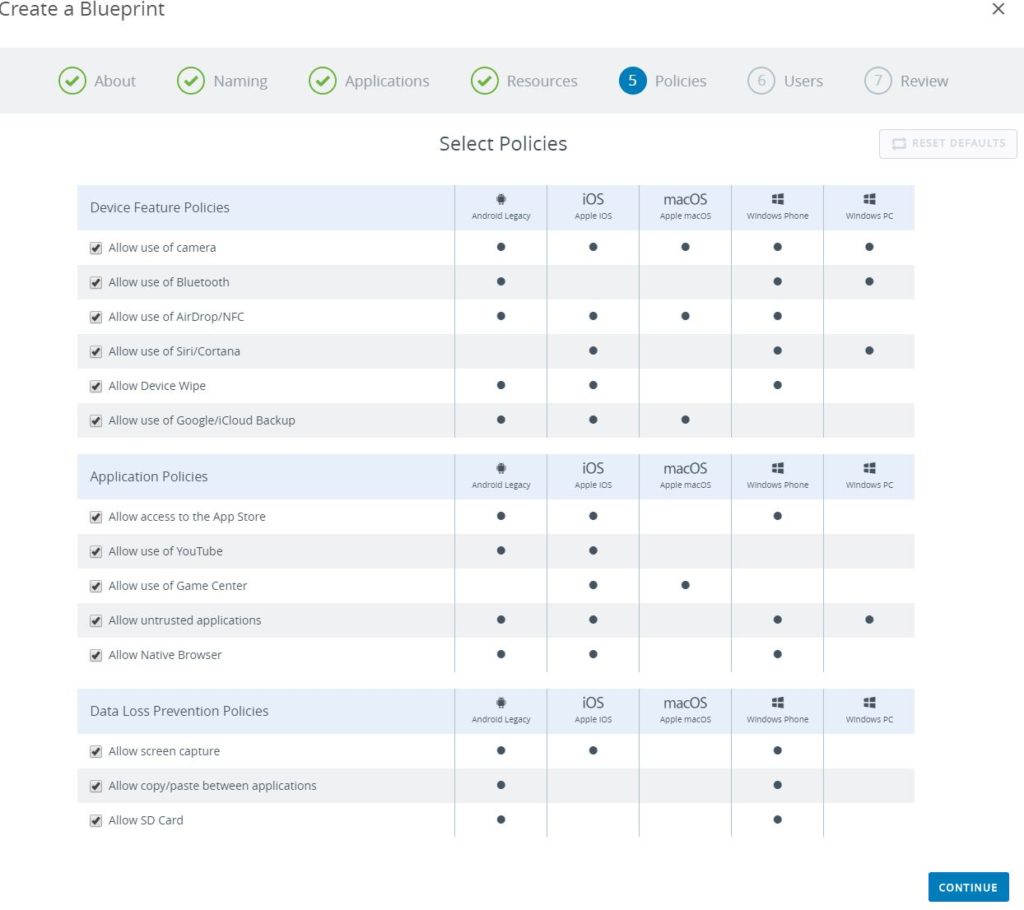
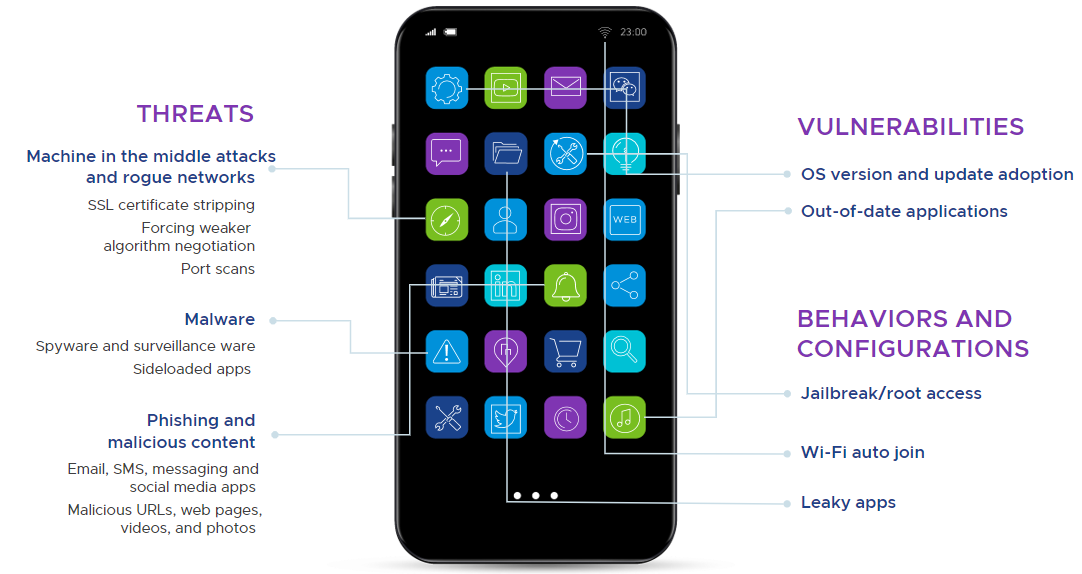
WS1 MTD addresses the dangers of phishing and web content, threat, vulnerabilities, and behaviors unique to mobile (Android, iOS, Chrome OS):
- Application-based threats including mobile malware, app vulnerabilities, and risky application behaviors and configurations
- Web and content vulnerabilities exposed through phishing via email, SMS, and messaging apps. This includes malicious URLs; malicious web pages, videos, and photos; and web and content behaviors and configurations
- Zero-day threats and device vulnerabilities including jailbreak and root access detection. Device risk including OS version and update adoption.
- Machine-in-the-middle attacks (MITM) and risky behaviors such as SSL certificate stripping; forcing weaker algorithm negotiation; anomalous application network connection activity; and vulnerabilities associated with rogue Wi-Fi
Integrated with Workspace ONE Intelligence, customers get these additional capabilities:
- Aggregate view of events across users and device types
- Interconnect endpoint, app, and identity analytics; CVE data; and threat data
- Automate remediation of devices back to secure and compliant state
- Flag users and devices for investigation and follow up
- Notify users of issues that require self remediation
Lookout has developed the Mobile Risk Matrix to help organizations understand the components and vectors that make up the spectrum of mobile risk:

How does it work?
This video provides a short and good explanation:
Product Components and Requirements
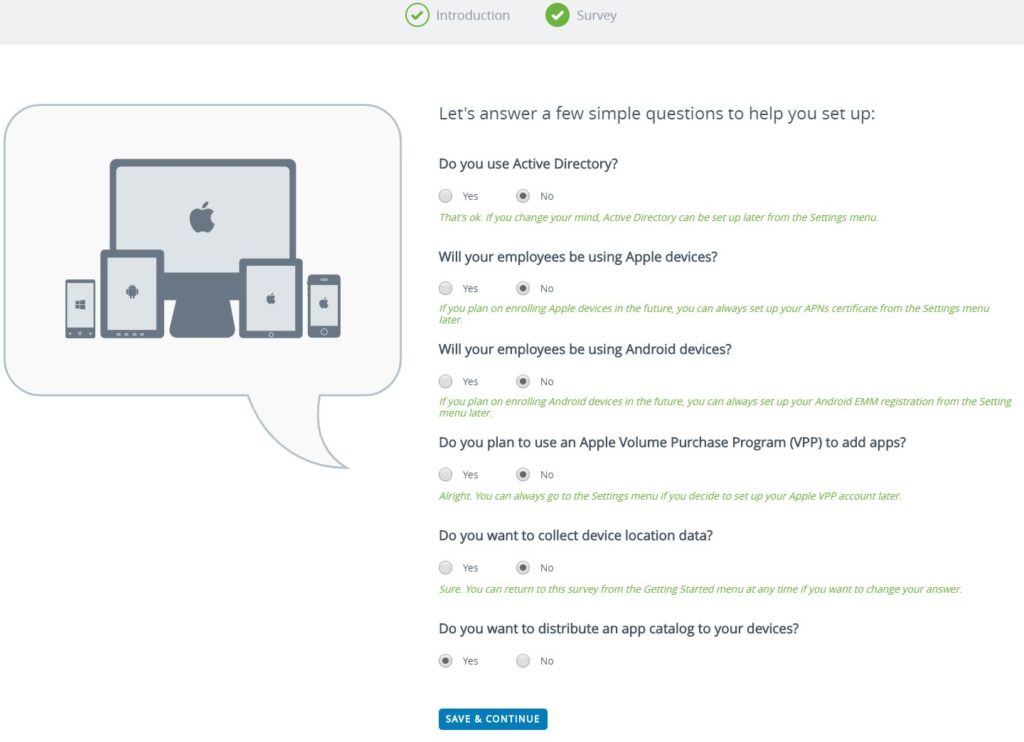
There are different components required to use Workspace ONE Mobile Threat Defense:
- WS1 MDT is available for Workspace ONE UEM on-premises, SaaS or managed hosting customers
- Workspace ONE Intelligent Hub 2204 or later
- Lookout for Work Mobile App is optional
- Only required for phishing and content protection, Android dual enrollment, and Chrome OS support
- Workspace ONE Intelligence is optional
- Required for customers that want to see threat data and use Intelligence’s automation engine
How to get Workspace ONE Mobile Threat Defense?
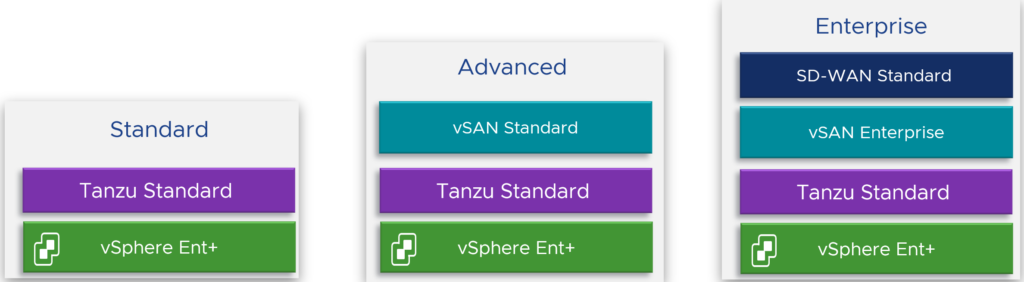
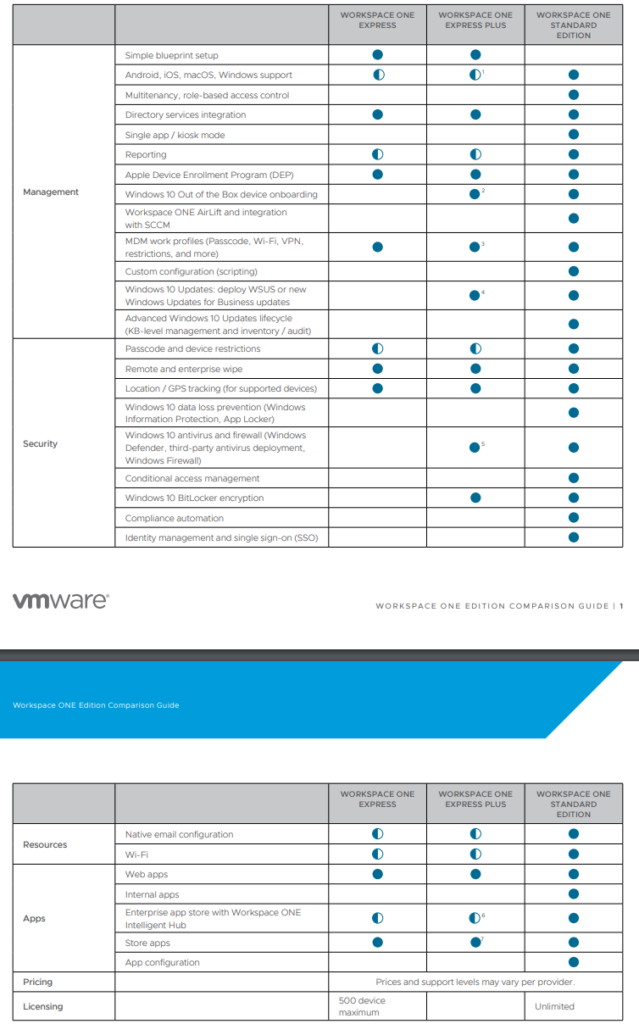
Workspace ONE Mobile Threat Defense is available with all Workspace ONE editions that deliver mobile management and UEM. This add-on SKU per device can be subscribed with these editions:
- Workspace ONE Mobile Essentials
- Workspace ONE UEM Essentials
- Workspace ONE Standard
- Workspace ONE Advanced
- Workspace ONE Enterprise
- Anywhere Workspace Enterprise
The Workspace ONE editions comparison datasheet can be found here.
Why VMware and Lookout?
Looking at the 2022 Gartner® Magic Quadrant™ for Unified Endpoint Management (UEM) Tools one can see that VMware scored highest in 4 out of 4 use cases in the 2022 Gartner® Critical Capabilities for UEM Tools.

Lookout has a huge install base with more than 200 million devices and was first in the industry to provide an enterprise mobile security product. Lookout’s demonstrated track of record of continuous innovation creates value for customers and a competitive advantage (they hold more than 175 patents!):
The Company also continued to enhance its market-leading Mobile Threat Defense solution – Lookout Mobile Endpoint Security – with the release of two new innovative features: Mobile Endpoint Detection and Response (mEDR) and Protective DNS for iOS and Android platforms. Mobile EDR is used to detect and investigate threats on mobile endpoints through real-time continuous monitoring and endpoint data analytics. Protective DNS encrypts DNS queries and implements safeguards to prevent users from accessing domains associated with phishing, malware, botnets, and other high-risk categories before a connection to the endpoint can be established.
Want a Test Drive?
If you want to test Workspace ONE Mobile Threat Defense, have a look at this TestDrive knowledge base article.