VCP Application Modernization 2022 Exam Review
It’s a PASS! I can call myself a VMware Certified Professional in Application Modernization (VCP-AM) now.
Some of you have seen it probably already on Twitter or LinkedIn (on January 20, 2022) – my goal for 2022 is to pass the following exams even I haven’t got hands-on experience with most the related products:
- VCP Application Modernization (VCP AM, 2V0-71.21)
- VCP Network Virtualization (VCP-NV)
- VCAP Data Center Virtualization Design (VCAP-DCV Design)
Why? Because I would like to achieve my 4th and 5th VCP and my 2nd VCAP certification. Last year I was very busy with my family, work and blogging. In 2022 I would like to achieve new certifications which are outside of my comfort zone and practical knowledge domain.
So, how did I pass the VCP-AM only three days later?
First, I rescheduled my exam date from March 3rd to February 3rd. This would have left me two weeks of preparation and I really thought I wouldn’t pass it at the first attempt. But I said to myself it is okay to fail the exam and trying to memorize the questions I struggled the most with.
Then I said: “I don’t need to wait for two weeks to figure that out! Let’s reschedule the exam once more and give it a try on Sunday (January 23rd).” This was the same approach I took back in 2018 when I was going for the VCAP-DTM Design exam (but there I missed a few points and failed).
Well…This time it worked out! 😀
About the VCP-AM Exam
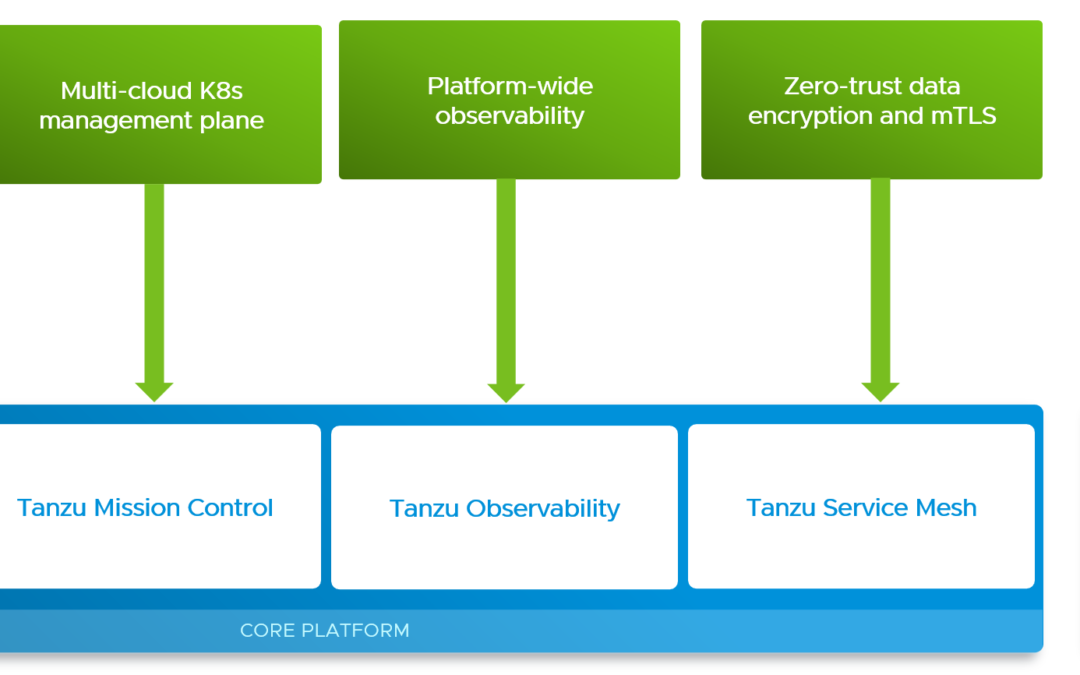
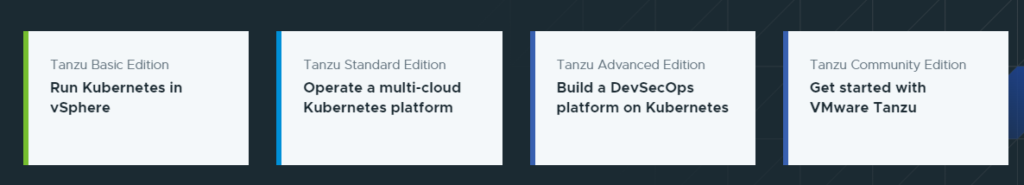
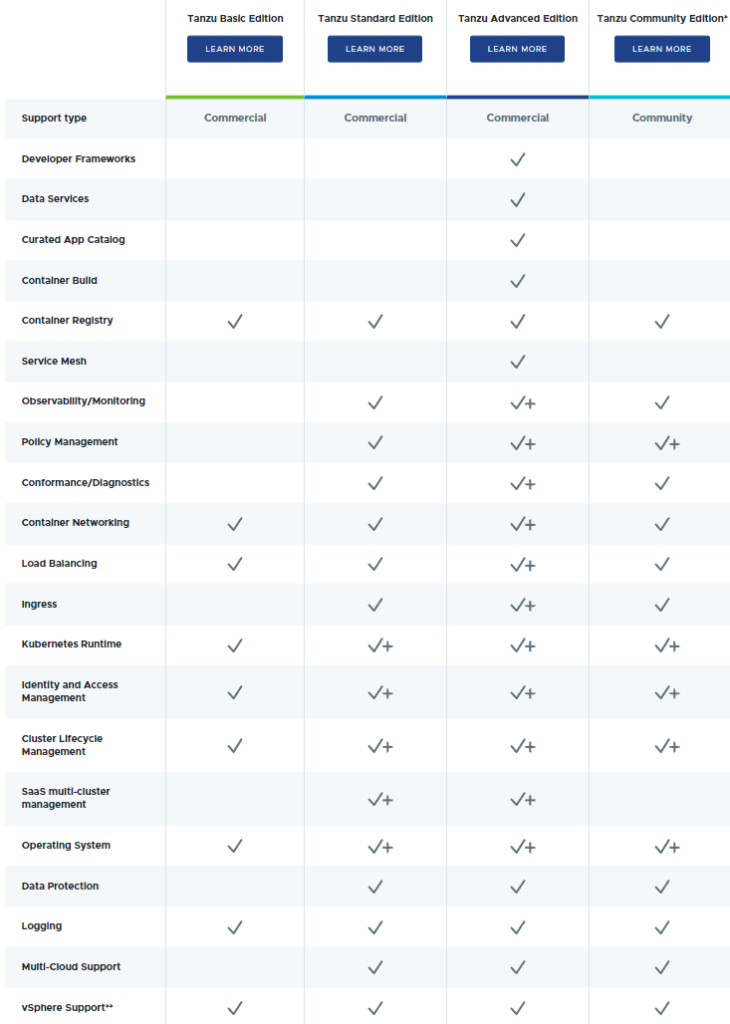
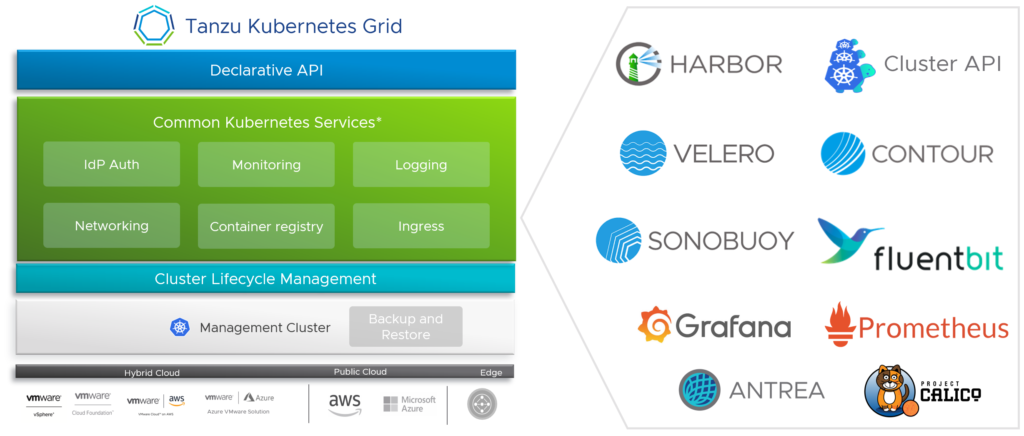
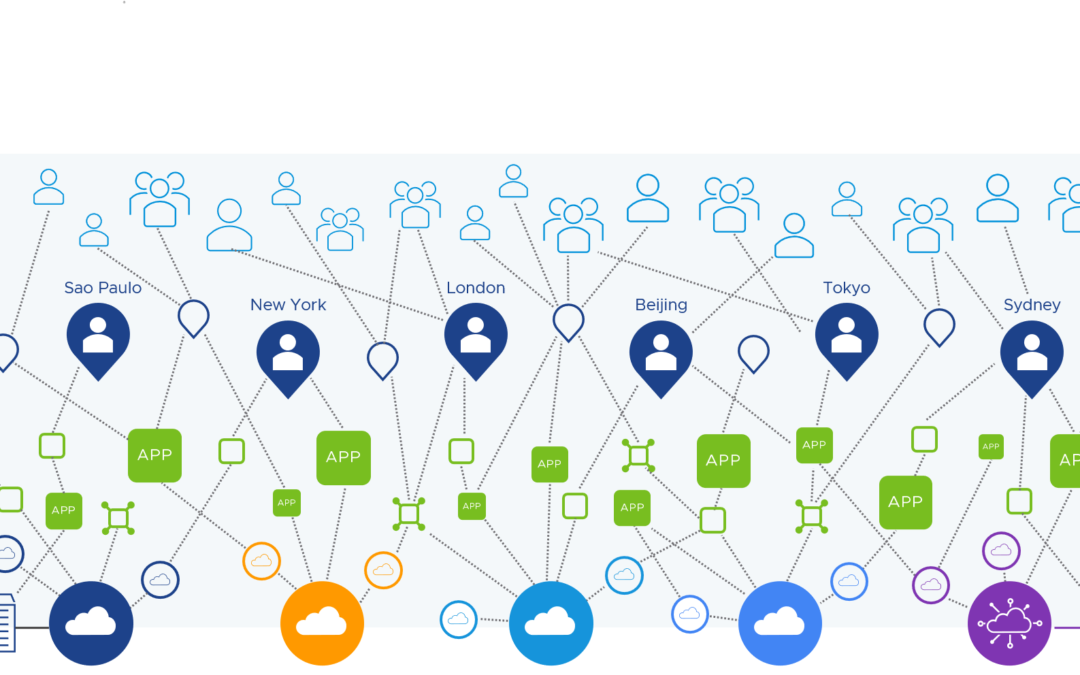
The certification validates your expertise with the VMware Tanzu Standard edition including vSphere with Tanzu, Tanzu Kubernetes Grid (TKG) and Tanzu Mission Control (TMC). If you look at the exam guide then you can see that this exam also checks your fundamental cloud native skills including containerization, application modernization and Kubernetes.
The VCP Application Modernization exam consists of 55 questions and must be completed within 130 minutes.
Certification Path
I hold three different VCP certifications (VCP-DCV, VCP-DTM, VCP-DW) so my steps look like this:
- (Recommended) Gain experience with VMware Tanzu
- (Recommended) Attend ONE of the training courses
- (Required) Pass the Professional VMware Application Modernization exam
Preparing for the Exam
The first step is about gaining experience with VMware Tanzu. Let me quickly list what I’ve done over the past two years:
- Was one of the first public speakers in Switzerland to present Project Pacific (today known as vSphere with Tanzu or TKGS) and also blogged about it.
- I think it was Q1 2020 when Project Pacific was available as an early private and then released as an official beta program. Was lucky enough to the get access to the installer files to enable “Workload Management” in my home lab. 🙂
- The year 2020 was about understanding Tanzu, its components, the different flavours (TKG aka TKGm, TKGS, TKGi) and editions
- In 2021 I ran two vSphere with Tanzu Standard PoCs with the help of some VMware Tanzu specialists. This was the time where I learned the most since the customers were very demanding and requested a lot of technical information. I also did a lot of blogging.
I think with this experience I already had the first step completed without realizing first how much experience I already had as a VMware employee!
If you have a home lab and can work (almost) on a daily basis with the Tanzu Standard products including Tanzu Mission Control, then I believe you have very good chances to pass the VCP application modernization exam as well. The exam guide is saying this:
The minimally qualified candidate (MQC) is recommended to have at least 6 to 12 months of experience. The MQC can
understand and describe standard features and capabilities of VMware Tanzu Standard Edition components including
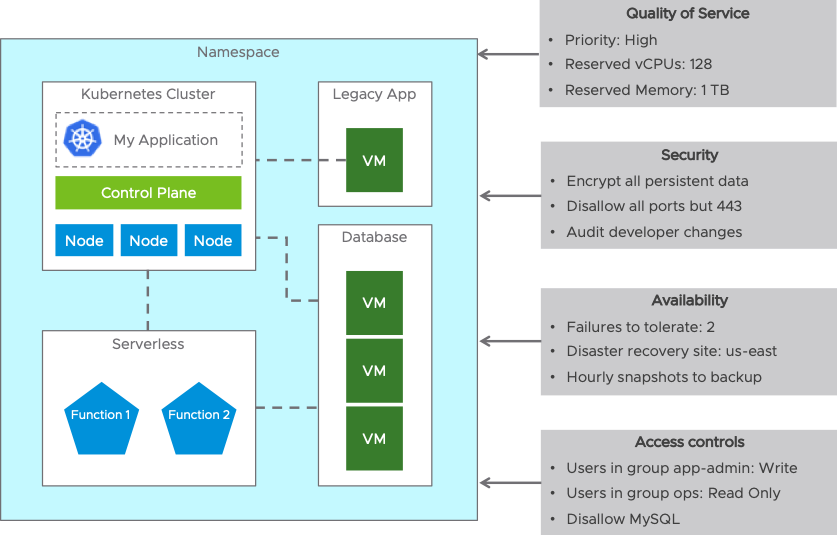
VMware vSphere with Tanzu, VMware Tanzu Kubernetes Grid, and VMware Tanzu Mission Control. The MQC can explain the VMware Tanzu vision and has hands-on experience with containerization, Kubernetes, and Application Modernization concepts. The MQC can perform common operational and administrative tasks in an environment where Tanzu Standard Edition Components are present, including basic troubleshooting and repairing of TKG clusters. The MQC can identify the primary components and features of Tanzu Mission Control but not limited to cluster lifecycle management, Role Based Access Controls, security policies, cluster inspections and data protection. In addition, the MQC can understand and describe the steps for installation and setup of Tanzu Standard Edition Components.
The MQC works in environments where VMware Tanzu Kubernetes Grid, vSphere with Tanzu and Tanzu Mission Control are used in production. The MQC can perform troubleshooting and repairing of TKG and TKC clusters. The MQC can identify the primary components and features of Tanzu Mission Control but not limited to cluster lifecycle management, Role Based Access Controls, security policies, cluster inspections and data protection. The MQC can perform day-2 operations related to TKG and TKC clusters. A successful candidate has a good grasp of the topics included in the exam blueprint.
Step 2 – Attend ONE of the Training Courses
While it’s not mandatory, it is still recommended to attend at least one of the official training courses:
- Kubernetes Foundations
- Kubernetes Fundamentals and Cluster Operations
- VMware Tanzu Kubernetes Grid: Install, Configure, Manage [V1.3]
- VMware vSphere with Tanzu: Deploy and Manage [V7]
- VMware Tanzu Mission Control: Management and Operations 2020
I recommend booking a training (if you need one), that includes TMC. People will have difficulties to get access to a Tanzu Mission Control cloud service. vSphere with Tanzu and Tanzu Kubernetes Grid are products that you easily can get access to and evaluate. Don’t forget to browse through the application modernization hands-on labs (HOLs)!
The most important resources for me were:
- The official VMware Tanzu Kubernetes Grid Documentation
- vSphere with Tanzu Configuration and Management (PDF)
- VMware Tanzu Mission Control Concepts (PDF)
- Using VMware Tanzu Mission Control (PDF)
Additional Resources
Besides the official trainings and HOLs, you can also get helpful and valuable information from these awesome bloggers:
- VMware Tanzu Mission Control – Getting started with your first cluster by Dean Lewis
- Tanzu Mission Control – Policies by Rudi Martinsen
- Tanzu Mission Control – Data Protection by Rudi Martinsen
- Tanzu Mission Control – Creating Clusters by Rudi Martinsen
- Tanzu Mission Control – Attaching Clusters by Rudi Martinsen
- Getting Started with Kubernetes by Eric Shanks
- Tanzu Mission Control Getting Started Guide by Eric Shanks
- vSphere 7 with Tanzu – Getting Started Guide by Eric Shanks
Please let me know if you found or used any other helpful resources which should be mentioned. Thanks.
Good Luck! 🙂